Abstract
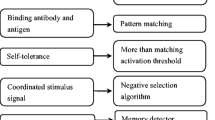
This paper briefly reviews other people’s works on negative selection algorithm and their shortcomings. With a view to the real problem to be solved, authors bring forward two assumptions, based on which a new immune algorithm, multi-level negative selection algorithm, is developed. In essence, compared with Forrest’s negative selection algorithm, it enhances detector generation efficiency. This algorithm integrates clonal selection process into negative selection process for the first time. After careful analyses, this algorithm was applied to network intrusion detection and achieved good results.
Similar content being viewed by others
References
DARPA, 1999. Intrusion Detection Evaluation. http://www.ll. mit.edu/IST/ideval/index.html.
Dasgupta, D., Gonzalez, F., 2002. An immunity-based technique to characterize intrusions in computer networks.IEEE Trans on Evolutionary Computation,6(3):281–291.
de Castro, L.N., Von Zuben, F.J., 1999. Artificial Immune Systems: Part I-Basic Theory and Applications. Technical Report-RT DCA 01/99, FEEC/Univ. Campinas, Campinas, Brazil. http://www.dca.fee.unicamp.br/~lnunes/immune.html.
Denning, D., 1987. An intrusion-detection model.IEEE Trans. Software Eng.,13:222–232.
D’haeseleer, P., Forrest, S., Helman, P., 1996. An Immunological Approach to Change Detection: Algorithms, Analysis and Implications. Proceedings of the 1996 IEEE Symposium on Research in Security and Privacy, IEEE Computer Society Press, Los Alamitos, CA.
Forrest, S., Perelson, A., Allen, L., Cherukuri, R., 1994. Self-Nonself Discrimination in A Computer. Proc. of the IEEE Symposium on Research in Security and Privacy, Oakland, CA, USA, p. 202–212.
Forrest, S., Hofmeyr, S.A., Somayaji, A., 1996. A Sense of self for UNIX Processes. Proceedings of the 1996 IEEE Symposium on Research in Security and Privacy, IEEE Computer Society Press, Los Alamitos, CA.
Forrest, S., Hofmeyr, S., Somayaji, A., 1997, Computer immunology.Communications of the ACM,40(10):88–96.
Harmer, P.K., Williams, P.O., Gunsch, G.H., Lamont, G.B., 2002. An artificial immune system architecture for computer security applications.IEEE Transactions on Evolutionary Computation,6(3):252–280.
Heberlein, L.T., Dias, G.V., Levitt, K.N., Mukherjec, B., Wood, J., Wolber, D., 1990. A Network Security Monitor. Proceedings of the IEEE Symposium on Security and Privacy, IEEE Press.
Hofmeyr, S.A., 1999. An Immunological Model of Distributed Detection and Its Application to Computer Security, Ph. D. Dissertation, University of New Mexico.
Hunt, J.E., Cooke, D.E., 1996. Learning using an artificial immune system.Journal of Network and Computer Applications, p. 189–212.
Kim, J., Bentley, P.J., 2001. Evaluating Negative Selection in An Artificial Immune System for Network Intrusion Detection. Genetic and Evolutionary Computation Conference 2001 (GECCO-2001), San Francisco, p. 1330–1337.
Perelson, A.S., Weisbuch, G., 1997. Immunology for Physicists.Rev. of Modern Physics,69(4):1219–1265.
Author information
Authors and Affiliations
Rights and permissions
About this article
Cite this article
Feng, P., Yun-fei, D. & Wei-nong, W. An immunity-based technique to detect network intrusions. J. Zheijang Univ.-Sci. A 6, 371–377 (2005). https://doi.org/10.1631/jzus.2005.A0371
Received:
Revised:
Published:
Issue Date:
DOI: https://doi.org/10.1631/jzus.2005.A0371