Abstract
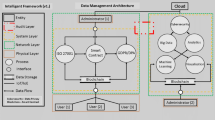
Epidemiologically investigating, such as COVID-19, means navigating through tight schedules, urgent tasking, and heavy workloads, hence the need for multi-department cooperation. However, a large amount of survey data contains private information which must also be shared among multiple departments. Therefore, it is necessary to ensure the confidentiality, integrity and availability of epidemiological data. To address the above problems, we propose a lightweight multi-departmental data sharing scheme by combining ciphertext-policy attribute-based encryption on elliptic curve, certificateless signature and consortium chain technology. In our scheme, elliptic curves are introduced into the ciphertext-policy attribute-based encryption to achieve fine-grained access control of shared data in multiple departments. Each department administrator generates an anonymous identity for each data owner to achieve identity conditional privacy. Furthermore, the data owner, during submission, generates a signature based on the certificateless technology, which safeguards the integrity of the shared survey data and avoids certificate management and key escrow problems along with a batch verification algorithm to improve the signature verification efficiency. Finally, it adopts consortium chain to store the signature information to prevent signature data tampering and enable public integrity auditing. Theoretical analysis and simulation experiments show its significant advantages over related ones in computation and storage overhead.










Similar content being viewed by others
Data availability
All relevant data are within the paper.
References
He, HY, Wu WS, Zhao Y, Wei ZF, Zhang GP, Fei CN (2021) Advances in the application of different information sources in the epidemiological investigation of COVID-19. Occupation a-nd Health, 37(5):694–697,702. https://doi.org/10.13329/j.cnki.zyyjk.2021.0176
Zhu WJ, Jin W, Huang Y, Xie CH, Wang FB (2021) Practice and experience of epidemiological investigation of new coronary pneumonia. People’s Army Medical 64(12):1313–1316. https://doi.org/10.3760/cma.j.cn112137-20211216-02803
Tabrizchi H, Kuchaki Rafsanjani M (2020) A survey on security challenges in cloud computing: issues, threats, and sol-utions. J Supercomput. https://doi.org/10.1007/s11227-020-03213-1
Jin L, Zhang YH, Cheng XF (2018) Secure attribute-based data sharing for resource-limited users in cloud computi-ng. Comput Secur 72:1–12. https://doi.org/10.1016/j.cose.2017.08.007
Ma C, Yan Z, Chang WC (2018) Scalable Access Con-trol for Privacy-Aware Media Sharing. IEEE Trans Multimedia 20(10):2834–2846. https://doi.org/10.1109/TMM.2018.2851446
Li H, Deng L, Yang C, Liu J (2020) An enhanced me-dia ciphertext-policy attribute-based encryption algorithm on media cloud. International Journal of Distributed Sensor Netw-orks 16(2):1550147720908196. https://doi.org/10.1177/1550147720908196
Li T, Zhang JW, Lin YX (2021) Blockchain-Based Fine-Grained Data Sharing for Multiple Groups in Internet of Things. Security and Communication Networks. https://doi.org/10.1155/2021/6689448
Odelu V, Das AK (2016) Design of a new CP-ABE with constant-size secret keys for lightweight devices using elliptic curve cryptography. Security & Communication Networks 9(17):4048–4059. https://doi.org/10.1002/sec.1587
Ding S, Li C, Li H (2018) A Novel Efficient Pairing-Free CP-ABE Based on Elliptic Curve Cryptography for IoT. IEEE ACCESS 6:27336–27345. https://doi.org/10.1109/ACCESS.2018.2836350
Shen WT, Qin J, Yu J, Hao R, Hu J (2018) Enabling identity-based integrity auditing and data sharing with sensitive information hiding for secure cloud storage. IEEE Trans Inf Forensics Secur. https://doi.org/10.1109/TIFS.2018.2850312
Neenu G, Seema B, Neeraj K (2020) An efficient data integrity auditing protocol for cloud computing, Future Generation C-omputer Systems. https://dio.org/https://doi.org/10.1016/j.future.2020.03.032
Shivarajkumar H, R. Sanjeev K. (2020) Homomorphic au-thentication scheme for proof of retrievability with public verifiability. In International Conference on Intelligent Computing and Control Systems. https://doi.org/10.1109/ICICCS48265.2020.9120974
Cong W, Sherman SM, Qian W (2010) Privacy-Preserving Public Auditing for Data Storage Security in Cloud Com-puting. In Int Con Comput Commun (INFOCOM), IEEE. https://doi.org/10.1109/TC.2011.245.
Shen J, Zhou T, Chen X, Li J, Susilo W (2018) Anon-ymous and Traceable Group Data Sharing in Cloud Computing. IEEE Trans Inf Forensics Secur 13(4):912–925. https://doi.org/10.1109/TIFS.2017.2774439
Huang H, Chen X, Wang J (2020) Blockchain-based m-ultiple groups data sharing with anonymity and traceability. Sc-ience China Inf-ormation Sciences. https://doi.org/10.1007/s11432-018-9781-0
Hong H, Sun Z (2022) TS-ABOS-CMS: time-bounded s-ecure attribute-based online/offline signature with constant me-ssage size for IoT systems. J Syst Archi 123, 102388. https://doi.org/10.1016/j.sysarc.2021.102388
Xiang D, Li X, Gao J, Zhang X (2022) A secure and efficient certificateless signature scheme for internet of things. Adhoc Net 124. https://doi.org/10.1016/j.adhoc.2021.102702
Huang H, Li KC, Chen XF (2018) Blockchain-based fair thr-ee-party contract signing protocol for fog computing. Concurr Comput Pract Exp 28, e4469. https://doi.org/10.1002/cpe.4469
Yang CS, Chen XF, Xian Y (2018) Blockchain-based public-ly verifiable data deletion scheme for cloud storage. J Net Comput Appli 103:185–193. https://doi.org/10.1016/j.jnca.2017.11.011
Liang J, Han WL, Guo ZQ (2018) DESC: enabling s-ecure da-ta exchange based on smart contracts. Sci Chin (Information Sciences) 61(4):049102. https://doi.org/10.1007/s11432-017-9245-1
Edoardo G, Leonardo A, Roberto B (2017) Blockchain-based d-atabase to ensure data integrity in cloud computing en-vironments. In Proceed Ital Confer Cybersec 146–155. https://doi.org/10.23919/ICOMBI48604.2020.9203500
Hong H, Sun Z (2021) A secure peer to peer multiparty tra-nsaction scheme based on blockchain. Peer-to-Peer Netw Ap-pl 14:1106–1117. https://doi.org/10.1007/s12083-021-01088-4
Ghoshal S, Paul G (2016) Exploiting blockchain data str-ucture for auditorless auditing on cloud data. In Int Conf e-Bus Inf Syst Sec 359–371. https://doi.org/10.1007/978-3-319-49806-5_19
Ongaro D, Ousterhout J (2014) In search of an understan-dable consensus algorithm. In Proceedings of the 2014 USENIX Conference on USENIX Annual Technical Conference (pp. 305–320). USA: USENIX Association. https://doi.org/10.5555/2643634.2643666
Meng WT, Zhang DW (2021) Optimization scheme for Hyper-ledger Fabric consensus mechanism. Acta Automatica Sinica 47(8):1885–1898. https://doi.org/10.16383/j.aas.c190516
Manvi SS, Kakkasager MS, Pitt J (2009) Multiagent based information dissemination in vehicular ad hoc networks. Mob Inf Syst 5:363–389. https://doi.org/10.1155/2009/518042
Huang JL, Yeh LY, Chien HY (2011) ABAKA: An anony-mous batch authenticated and key agreement scheme for value-added services in vehicular ad hoc networks. IEEE Tra-nsactions on Vehicular Technology 60:248–262. https://doi.org/10.1109/TVT.2010.2089544
Pointcheval D, Stern J (2000) Security arguments for dig-ital signatures and blind signatures. J Cryptol 13(3):361–396. https://doi.org/10.1007/s00145-001-0003-0
Zhou YW, Yang B, Zhang WZ (2015) Efficient and secure certificateless aggregate signature scheme. J Software 26(12):3204–3214. https://doi.org/10.13328/j.cnki.jos.004830
Tang YL, Wang FF, Ye Q (2016) Improved provably secure certificateless signature scheme. J Beijing Univ Posts Telecommun 39(1):112–116. https://doi.org/10.13190/j.jbupt.2016.01.021
Wu LB, Xie Y, Zhang YB (2016) Efficient and secure message authentication scheme for VANET. J Commun 37(11):1–10. https://doi.org/10.11959/j.issn.1000-436x.2016211
Liu X, Wang L, Huan L, Du X, Niu S (2022) Certifi-cateless anonymous authentication scheme for Internet of Vehicles. J Electron Sci Technol 44(1):295–304. https://doi.org/10.11999/JEIT201069
Odelu V, Das AK (2016) Design of a new CP-ABE with constant-size secret keys for lightweight devices using elliptic curve cryptography. Security Comm Networks 9:4048–4059. https://doi.org/10.1002/sec.1587
Lewko A, Waters B (2011) Decentralizing Attribute-Based Encryption. In: Paterson, K.G. (eds) Advances in Cryptology – EUROCRYPT 2011. EUROCRYPT 2011. Lecture Notes in Comput Sci 6632. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-20465-4_31
Liang G, Weller SR, Luo F, Zhao J, Dong ZY (2019) Distributed blockchain-based data protection framework for modern power systems against cyber-attacks. IEEE Transacti-ons on Smart Grid 10(3):3162–3173. https://doi.org/10.1109/TSG.2018.2819663
Funding
The work was supported by Foundation Items: The National Natural Science Foundation of China (No. 62262060, 61662071, 62241207); Industrial support plan project of Gansu Provincial Department of Education (2022CYZC-17); Gansu Science and Technology Program(22JR5RA158).
Author information
Authors and Affiliations
Contributions
Xueyan Liu and Linpeng Li wrote the main manuscript text and Ruirui Sun, Wenjing LI, Tao Liu supervised and analyzed the scheme.
Corresponding author
Ethics declarations
Ethics approval
Not applicable.
Consent to publish
The authors agree to publish this work.
Conflict of interest
The authors declare that they have no conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This article is part of the Topical Collection: Special Issue on 2 - Track on Security and Privacy
Guest Editor: Rongxing Lu
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Liu, X., Li, L., Sun, R. et al. Lightweight multi-departmental data sharing scheme based on consortium blockchain. Peer-to-Peer Netw. Appl. 16, 2399–2414 (2023). https://doi.org/10.1007/s12083-023-01523-8
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-023-01523-8