Abstract
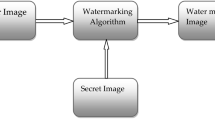
A novel multiple watermarks cooperative authentication algorithm was presented for image contents authentication. This algorithm is able to extract multiple features from the image wavelet domain, which is based on that the t watermarks are generated. Moreover, a new watermark embedding method, using the space geometric model, was proposed, in order to effectively tackle with the mutual influences problem among t watermarks. Specifically, the incidental tampering location, the classification of intentional content tampering and the incidental modification can be achieved via mutual cooperation of the t watermarks. Both the theoretical analysis and simulations results validate the feasibility and efficacy of the proposed algorithm.
Similar content being viewed by others
References
MINTZER F, BRAUDAWAY G W. If one watermark is good, are more better [C]// Proceedings of the International Conference on Acoustics, Speech, and Signal Processing, Kobe, Japan: IEEE Press, 1999: 2067–2070.
BADRAN E F, SHARKAS M A, ATTALLAH O A. Multiple watermark embedding scheme in wavelet-spatial domains based on ROI of medical images [C]// National Radio Science Conference (NRSC 2009), Cairo: IEEE Press, 2009: 1–8.
COX I J, MILLER M L. Digital watermarking [M]. New York: Academic Press, 2002: 248–253.
STANKOVIC S, DJUROVIC I, PITAS I. Watermarking in the space/spatial frequency domain using two-dimensional Radon-Wigner distribution [J]. IEEE Transactions Image Processing, 2001, 10(4): 650–658.
LIE W N, LIN G N, WU C L, WANG T C. Robust image watermarking on the DCT domain [C]// Proc IEEE Int Symp Circuits and Systems, Geneva: IEEE Press, 2000, 1(5): 228–231.
PETER H W, OSCAR C A, YEUNG Y M. A novel blind multiple watermarking technique for images [J]. IEEE Transactions on Circuits and Systems for Video Technology, 2003, 8(13): 813–830.
HSU C T, WU J L. Hidden digital watermarks in images [J]. IEEE Transactions on Image Processing, 1999, 8(1): 58–68.
JI Z, XIAO W W, WANG J H, ZHANG J H. A multiple watermarking algorithm for digital image based on chaotic sequences [J]. Chinese Journal of Computers, 2003, 11(26): 1555–1561.
BOATO G, DE NATALE F G B, FONTANARI C. Digital image tracing by sequential multiple watermarking [J]. IEEE Transactions on Multimedia, 2007, 9(4): 677–686.
MOHAMED A, ABOU-SOUD M A, DIAB M S. Implementation of fast digital watermarking techniques [C]// International Conference on Computer Engineering & Systems, Cairo: IEEE Press, 2008: 419–426.
JIN C, SU T, PAN L G. Multiple digital watermarking scheme based on ICA [C]// Image Analysis for Multimedia Interactive Services (WlAMIS’07), Santorini: IEEE Press, 2007: 70–76.
JENG-SHYANG, PAN, HSIANG-CHEH HUANG, FENG-HSING WANG. A VQ-based robust multi-watermarking algorithm [C]// In Proceedings 2002 IEEE Region Conference on Computers, Communications, Control and Power Engineering, Beijing: IEEE Press, 2002: 117–120.
LUO H, PAN J S, LU Z M. Hiding multiple watermarks in transparencies of visual cryptography [C]// Third International Conference on Intelligent Information Hiding and Multimedia signal Processing, Harbin: IEEE Press, 2007: 303–306.
LAI C C, HUANG H C, TSAI C C. Image watermarking scheme using singular value decomposition and micro-genetic algorithm [C]// The 4th International Conference on Intelligent Information Hiding and Multimedia Signal Processing, Harbin: IEEE Press, 2008: 469–472.
NASIR I, WENG Y, JIANG J M. Novel multiple spatial watermarking technique in color images [C]// 5th International Conference on Information Technology: New Generations, Las Vegas: IEEE Press, 2008: 777–782.
HUANG W, GOU J. An image fusion-based multi-watermarking algorithm [C]// Proceedings of the 2006 IEEE International Conference on Networking, Sensing and Control(ICNSC’06), Florida: IEEE Press, 2006: 266–269.
HAMMERLE-UHL J, LIEDLGRUBER M, UHL A, WEMISCH H. Multiple re-watermarking using varying wavelet packets [C]// 2008 IEEE International Conference on Multimedia and Expo, Hannover: IEEE Press, 2008: 213–216.
LU C S, MARK H Y. Multipurpose watermarking for image authentication and protection [J]. IEEE Trans on Image Processing, 2001, 10(10): 1579–1592.
LU C S, HSU C Y. Content-dependent multipurpose watermarking resistant against generalized copy attack [C]// IEEE International Conference on Multimedia and Expo (ICME), Taipei: IEEE Press, 2004: 2039–2042.
DONOHO D L. Denoising by soft thresholding [J]. IEEE Transactions on Information Theory, 1995, 41(3): 613–627.
CHANG S G, YU B, VETTERI M. Spatially adaptive wavelet thresholding with context modeling for image denosing [J]. IEEE Transactions on Image Processing, 2000, 9(10): 1522–1531.
HU Yun-quan. Operational research tutorial (second edition) [M]. Beijing: Tsinghua University Press, 2003: 436–446. (in Chinese)
Author information
Authors and Affiliations
Corresponding author
Additional information
Foundation item: Project(2012BAH09B02) supported by the National Science and Technology Support Program, China; Projects(12JJ3068, 12JJ2041) supported by the Natural Science Fundation of Hunan Province, China
Rights and permissions
About this article
Cite this article
Cai, Lj., Li, R. & Yi, Yq. A multiple watermarks algorithm for image content authentication. J. Cent. South Univ. 19, 2866–2874 (2012). https://doi.org/10.1007/s11771-012-1353-2
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11771-012-1353-2