Abstract
In a quantum Trojan-horse attack (THA), eavesdroppers learn encoded information by injecting bright light into encoded or decoded devices of quantum key distribution (QKD) systems. These attacks severely compromise the security of non-isolated systems. Thus, analytical security bound was derived in previous studies. However, these studies achieved poor performance unless the devices were strongly isolated. Here, we present a numerical method for achieving improved security bound for a decoy-state QKD system under THAs. The developed method takes advantage of the well-established numerical framework and significantly outperforms previous analytical bounds regarding the achievable final key and secure transmitted distance. The results provide a new tool for investigating the efficient security bounds of THA in practical decoy-state QKD systems. This study constitutes an important step toward securing QKD with real-life components.



Similar content being viewed by others
Data availability
Data will be made available on reasonable request
References
Bennett , C.H., Brassard, G. et al.: In: Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, Quantum cryptography: Public Key Distribution and Coin Tossing. vol. 175, New York (1984)
Wang, S., Chen, W., Guo, J.-F., Yin, Z.-Q., Li, H.-W., Zhou, Z., Guo, G.-C., Han, Z.-F.: 2 GHz clock quantum key distribution over 260 km of standard telecom fiber. Opt. Lett. 37, 1008 (2012)
Cañas, G., Vera, N., Cariñe, J., González, P., Cardenas, J., Connolly, P.W.R., Przysiezna, A., Gómez, E.S., Figueroa, M., Vallone, G., Villoresi, P., da Silva, T.F., Xavier, G.B., Lima, G.: High-dimensional decoy-state quantum key distribution over multicore telecommunication fibers. Phys. Rev. A 96, 022317 (2017)
Islam, N.T., Lim, C.C.W., Cahall, C., Kim, J., Gauthier, D.J.: Provably secure and high-rate quantum key distribution with time-bin qudits. Sci. Adv. 3, e1701491 (2017)
Yuan, Z., Plews, A., Takahashi, R., Doi, K., Tam, W., Sharpe, A., Dixon, A., Lavelle, E., Dynes, J., Murakami, A., Kujiraoka, M., Lucamarini, M., Tanizawa, Y., Sato, H., Shields, A.J.: 10-Mb/s quantum key distribution. Lightw. Technol. 36, 3427 (2018)
Boaron, A., Boso, G., Rusca, D., Vulliez, C., Autebert, C., Caloz, M., Perrenoud, M., Gras, G., Bussières, F., Li, M.-J., Nolan, D., Martin, A., Zbinden, H.: Secure quantum key distribution over 421 km of optical fiber. Phys. Rev. Lett. 121, 190502 (2018)
Ma, D., Liu, X., Huang, C., Chen, H., Lin, H., Wei, K.: Simple quantum key distribution using a stable transmitter–receiver scheme. Opt. Lett. 46, 2152 (2021)
Huang, C., Chen, Y., Jin, L., Geng, M., Wang, J., Zhang, Z., Wei, K.: Experimental secure quantum key distribution in the presence of polarization-dependent loss. Phys. Rev. A 105, 012421 (2022)
Li, W., Zhang, L., Tan, H., Lu, Y., Liao, S.-K., Huang, J., Li, H., Wang, Z., Mao, H.-K., Yan, B., Li, Q., Liu, Y., Zhang, Q., Peng, C.-Z., You, L., Xu, F., Pan, J.-W.: High-rate quantum key distribution exceeding 110 Mb s\(^-1\). Nat. Photon. 17, 1 (2023)
Grunenfelder, F., Boaron, A., Resta, G.V., Perrenoud, M., Rusca, D., Barreiro, C., Houlmann, R., Sax, R., Stasi, L., El-Khoury, S., Hanggi, E., Bosshard, N., Bussieres, F., Zbinden, H.: Fast single-photon detectors and real-time key distillation enable high secret-key-rate quantum key distribution systems. Nat. Photon. 17, 422 (2023)
Du, Y., Zhu, X., Hua, X., Zhao, Z., Hu, X., Qian, Y., Xiao, X., Wei, K.: Silicon-based decoder for polarization-encoding quantum key distribution. Chip 2, 100039 (2023)
Wei, K., Hu, X., Du, Y., Hua, X., Zhao, Z., Chen, Y., Huang, C., Xiao, X.: Resource-efficient quantum key distribution with integrated silicon photonics. Photon. Res. 11, 1364 (2023)
Liao, S.-K., Cai, W.-Q., Liu, W.-Y., Zhang, L., Li, Y., Ren, J.-G., Yin, J., Shen, Q., Cao, Y., Li, Z.-P., et al.: Satellite-to-ground quantum key distribution. Nature 549, 43 (2017)
Chen, H., Wang, J., Tang, B., Li, Z., Liu, B., Sun, S.: Field demonstration of time-bin reference-frame-independent quantum key distribution via an intracity free-space link. Opt. Lett. 45, 3022 (2020)
Avesani, M., Calderaro, L., Schiavon, M., Stanco, A., Agnesi, C., Santamato, A., Zahidy, M., Scriminich, A., Foletto, G., Contestabile, G., Chiesa, M., Rotta, D., Artiglia, M., Montanaro, A., Romagnoli, M., Sorianello, V., Vedovato, F., Vallone, G., Villoresi, P.: Full daylight quantum-key-distribution at 1550 nm enabled by integrated silicon photonics. NPJ Quantum Inf. 7, 93 (2021)
Al-Juboori, A., Zeng, H.Z.J., Nguyen, M.A.P., Ai, X., Laucht, A., Solntsev, A., Toth, M., Malaney, R., Aharonovich, I.: Quantum key distribution using a quantum emitter in hexagonal boron nitride. Adv. Quantum Technol. 6, 2300038 (2023)
Sasaki, M., Fujiwara, M., Ishizuka, H., Klaus, W., Wakui, K., Takeoka, M., Miki, S., Yamashita, T., Wang, Z., Tanaka, A.: Field test of quantum key distribution in the Tokyo QKD network. Opt. Express 19, 10387 (2011)
Dynes, J.F., Wonfor, A., Tam, W.W.S., Sharpe, A.W., Takahashi, R., Lucamarini, M., Plews, A., Yuan, Z.L., Dixon, A.R., Cho, J., Tanizawa, Y., Elbers, J.P., Greißer, H., White, I.H., Penty, R.V., Shields, A.J.: Cambridge quantum network. NPJ Quantum Inf. 5, 101 (2019)
Wang, S., Chen, W., Yin, Z.-Q., Li, H.-W., He, D.-Y., Li, Y.-H., Zhou, Z., Song, X.-T., Li, F.-Y., Wang, D., Chen, H., Han, Y.-G., Huang, J.-Z., Guo, J.-F., Hao, P.-L., Li, M., Zhang, C.-M., Liu, D., Liang, W.-Y., Miao, C.-H., Wu, P., Guo, G.-C., Han, Z.-F.: Field and long-term demonstration of a wide area quantum key distribution network. Opt. Express 22, 21739 (2014)
Chen, Y.-A., Zhang, Q., Chen, T.-Y., Cai, W.-Q., Liao, S.-K., Zhang, J., Chen, K., Yin, J., Ren, J.-G., Chen, Z., Han, S.-L., Yu, Q., Liang, K., Zhou, F., Yuan, X., Zhao, M.-S., Wang, T.-Y., Jiang, X., Zhang, L., Liu, W.-Y., Li, Y., Shen, Q., Cao, Y., Lu, C.-Y., Shu, R., Wang, J.-Y., Li, L., Liu, N.-L., Xu, F., Wang, X.-B., Peng, C.-Z., Pan, J.-W.: An integrated space-to-ground quantum communication network over 4600 kilometres. Nature 589, 214 (2021)
Wang, S., Yin, Z.-Q., He, D.-Y., Chen, W., Wang, R.-Q., Ye, P., Zhou, Y., Fan-Yuan, G.-J., Wang, F.-X., Chen, W., Zhu, Y.-G., Morozov, P.V., Divochiy, A.V., Zhou, Z., Guo, G.-C., Han, Z.-F.: Twin-field quantum key distribution over 830-km fibre. Nat. Photon. (2022). https://doi.org/10.1038/s41566-021-00928-2
Diamanti, E., Lo, H.-K., Qi, B., Yuan, Z.: Practical challenges in quantum key distribution. NPJ Quantum Inf. 2, 16025 (2016)
Xu, F., Ma, X., Zhang, Q., Lo, H.-K., Pan, J.-W.: Secure quantum key distribution with realistic devices. Rev. Mod. Phys. 92, 025002 (2020)
Lo, H.-K., Curty, M., Tamaki, K.: Secure quantum key distribution. Nat. Photon. 8, 595 (2014)
Xu, F., Wei, K., Sajeed, S., Kaiser, S., Sun, S., Tang, Z., Qian, L., Makarov, V., Lo, H.-K.: Experimental quantum key distribution with source flaws. Phys. Rev. A 92, 032305 (2015)
Pereira, M., Kato, G., Mizutani, A., Curty, M., Tamaki, K.: Quantum key distribution with correlated sources. Sci. Adv. 6, 4487 (2020)
Makarov, V., Anisimov, A., Skaar, J.: Effects of detector efficiency mismatch on security of quantum cryptosystems. Phys. Rev. A (2006). https://doi.org/10.1103/PhysRevA.74.022313
Qi, B., Fred, F.C.-H., Lo, H.-K., Ma, X.: Time-shift attack in practical quantum cryptosystems. Quant. Inf. Comput. 7, 73 (2007)
Sajeed, S., Chaiwongkhot, P., Bourgoin, J.-P., Jennewein, T., Lütkenhaus, N.L., Makarov, V.: Security loophole in free-space quantum key distribution due to spatial-mode detector-efficiency mismatch. Phys. Rev. A 91, 062301 (2015)
Wei, K., Zhang, W., Tang, Y.-L., You, L., Xu, F.: Implementation security of quantum key distribution due to polarization-dependent efficiency mismatch. Phys. Rev. A 100, 022325 (2019)
Lydersen, L., Wiechers, C., Wittmann, C., Elser, D., Skaar, J., Makarov, V.: Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photon. 4, 686 (2010)
Xu, F., Qi, B., Lo, H.-K.: Experimental demonstration of phase-remapping attack in a practical quantum key distribution system. New J. Phys. 12, 113026 (2010)
Vakhitov, A., Makarov, V., Hjelme, D.R.: Large pulse attack as a method of conventional optical eavesdropping in quantum cryptography. J. Mod. Optic. 48, 2023 (2001)
Gisin, N., Fasel, S., Kraus, B., Zbinden, H., Ribordy, G.: Trojan-horse attacks on quantum-key-distribution systems. Phys. Rev. A (2006). https://doi.org/10.1103/PhysRevA.73.022320
Lo, H.-K., Chau, H.F.: Unconditional security of quantum key distribution over arbitrarily long distances. Science 283, 2050 (1999)
Gottesman, D., Lo, H.-K., Lütkenhaus, N.L., Preskill, J.: Security of quantum key distribution with imperfect devices. Quant. Inf. Comput. 4, 325 (2004)
Acín, A., Brunner, N., Gisin, N., Massar, S., Pironio, S., Scarani, V.: Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. (2007). https://doi.org/10.1103/PhysRevLett.98.230501
Schwonnek, R., Goh, K.T., Primaatmaja, I.W., Tan, E.Y.Z., Wolf, R., Scarani, V., Lim, C.C.W.: Device-independent quantum key distribution with random key basis. Nat. Commun. 12, 2880 (2021)
Xu, F., Zhang, Y.-Z., Zhang, Q., Pan, J.-W.: Device-independent quantum key distribution with random postselection. Phys. Rev. Lett. 128, 110506 (2022)
Jain, N., Stiller, B., Khan, I., Makarov, V., Marquardt, C., Leuchs, G.: Risk analysis of trojan-horse attacks on practical quantum key distribution systems. IEEE. J. Sel. Top. Quant. 21, 168 (2015)
Sajeed, S., Minshull, C., Jain, N., Makarov, V.: Invisible Trojan-horse attack. Sci. Rep. 7, 8403 (2017)
Tan, H., Li, W., Zhang, L., Wei, K., Xu, F.: Chip-based quantum key distribution against Trojan-horse attack. Phys. Rev. Appl. 15, 064038 (2021)
Nitin, J., Elena, A., Imran, K., Vadim, M., Christoph, M., Gerd, L.: Trojan-horse attacks threaten the security of practical quantum cryptography. New J. Phys. 16, 123030 (2014)
Ponosova, A., Ruzhitskaya, D., Chaiwongkhot, P., Egorov, V., Makarov, V., Huang, A.: Protecting Fiber-Optic Quantum Key Distribution Sources Against Light-Injection Attacks (2022). arXiv preprint arXiv:2201.06114
Lucamarini, M., Choi, I., Ward, M.B., Dynes, J.F., Yuan, Z.L., Shields, A.J.: Practical security bounds against the trojan-horse attack in quantum key distribution. Phys. Rev. X 5, 031030 (2015)
Tamaki, K., Curty, M., Lucamarini, M.: Decoy-state quantum key distribution with a leaky source. New J. Phys. 18, 065008 (2016)
Wang, W., Tamaki, K., Curty, M.: Finite-key security analysis for quantum key distribution with leaky sources. New J. Phys. 20, 083027 (2018)
Navarrete, A., Curty, M.: Improved Finite-Key Security Analysis of Quantum Key Distribution Against Trojan-Horse Attacks (2022). arXiv preprint arXiv:2202.06630
Wang, W., Tamaki, K., Curty, M.: Measurement-device-independent quantum key distribution with leaky sources. Sci. Rep. 11, 1678 (2021)
Lu, Y.-F., Wang, Y., Jiang, M.-S., Zhang, X.-X., Liu, F., Li, H.-W., Zhou, C., Tang, S.-B., Wang, J.-Y., Bao, W.-S.: Sending or not-sending twin-field quantum key distribution with flawed and leaky sources. Entropy 23, 1103 (2021)
Lo, H.-K., Ma, X., Chen, K.: Decoy state quantum key distribution. Phys. Rev. Lett. (2005). https://doi.org/10.1103/PhysRevLett.94.230504
Wang, X.-B.: Beating the photon-number-splitting attack in practical quantum cryptography. Phys. Rev. Lett. 94, 230503 (2005)
Braunstein, S.L., Pirandola, S.: Side-channel-free quantum key distribution. Phys. Rev. Lett. 108, 130502 (2012)
Lo, H.-K., Curty, M., Qi, B.: Measurement-Device-Independent Quantum Key Distribution. Phys. Rev. Lett. 108, 130503 (2012)
Wang, W., Lütkenhaus, N.: Numerical security proof for the decoy-state BB84 protocol and measurement-device-independent quantum key distribution resistant against large basis misalignment. Phys. Rev. Research 4, 043097 (2022)
Ferenczi, A., Lütkenhaus, N.: Symmetries in quantum key distribution and the connection between optimal attacks and optimal cloning. Phys. Rev. A 85, 052310 (2012)
Coles, P.J., Metodiev, E.M., Lütkenhaus, N.L.: Numerical approach for unstructured quantum key distribution. Nat. Commum. 7, 11712 (2016)
Winick, A., Lütkenhaus, N.L., Coles, P.J.: Reliable numerical key rates for quantum key distribution. Quantum 2, 77 (2018)
George, I., Lin, J., Lütkenhaus, N.L.: Numerical calculations of the finite key rate for general quantum key distribution protocols. Phys. Rev. Res. 3, 013274 (2021)
Bunandar, D., Govia, L.C.G., Krovi, H., Englund, D.: Numerical finite-key analysis of quantum key distribution. NPJ Quantum Inf. 6, 104 (2020)
Li, N.K.H., Lütkenhaus, N.: Improving key rates of the unbalanced phase-encoded BB84 protocol using the flag-state squashing model. Phys. Rev. Res. 2, 043172 (2020)
Scarani, V., Bechmann-Pasquinucci, H., Cerf, N.J., Dusek, M., Lutkenhaus, N., Peev, M.: The security of practical quantum key distribution. Rev. Mod. Phys. 81, 1301 (2009)
Lo, H.-K., Preskill, J.: Security of quantum key distribution using weak coherent states with nonrandom phases. Quant. Inf. Comput. 7, 431 (2006)
Liu, H., Wang, W., Wei, K., Fang, X.-T., Li, L., Liu, N.-L., Liang, H., Zhang, S.-J., Zhang, W., Li, H., You, L., Wang, Z., Lo, H.-K., Chen, T.-Y., Xu, F., Pan, J.-W.: Experimental demonstration of high-rate measurement-device-independent quantum key distribution over asymmetric channels. Phys. Rev. Lett. 122, 160501 (2019)
Sun, S., Xu, F.: Security of quantum key distribution with source and detection imperfections. New J. Phys. 23, 023011 (2021)
Acknowledgements
We thank Shi-Hai Sun and Wenyuan Wang for their helpful discussions. This study was supported by the National Natural Science Foundation of China (Nos. 62171144 and 62031024 and 11905065), the Guangxi Science Foundation (Nos. 2021GXNSFAA220011 and 2021AC19384), and the Open Fund of IPOC (BUPT) (No. IPOC2021A02).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
Appendix A: Measurement operator, Kraus operator, key mapping
In this section, we will describe the specific forms of operators required in BB84 and MDI protocols. Our protocol description model is similar to Ref. [55].
1.1 1 BB84
The measurement operator is:
\(P_{i}^{A}\) | \(|0\rangle \langle 0|\) | \(|1\rangle \langle 1|\) | \(|2\rangle \langle 2|\) | \(|3\rangle \langle 3|\) | |
|---|---|---|---|---|---|
\(P_{i}^{B}\) | \(|Z_{+} \rangle \langle Z_{+}| \oplus 0\) | \(|Z_{-} \rangle \langle Z_{-}|\oplus 0\) | \(|X_{+} \rangle \langle X_{+}|\oplus 0 \) | \(|X_{-} \rangle \langle X_{-}|\oplus 0\) | \( 1-\sum _{i=1}^{4}P_{i}^{B}\) |
The tomographic scanning operator is:
The Kraus operator is:
While the key maps are:
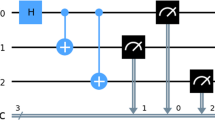
1.2 2 MDI
The measurement operator is
\(P_{i}^{A}\) | \(|0\rangle \langle 0|\) | \(|1\rangle \langle 1|\) | \(|2\rangle \langle 2|\) | \(|3\rangle \langle 3|\) |
|---|---|---|---|---|
\(P_{i}^{B}\) | \(|0\rangle \langle 0|\) | \(|1\rangle \langle 1|\) | \(|2\rangle \langle 2|\) | \(|3\rangle \langle 3|\) |
\(P_{i}^{C}\, \left| \Phi ^{+}\right\rangle _{a b}\left\langle \left. \Phi ^{+}\right| _{a b}\right. \, \left| \Phi ^{+}\right\rangle _{a b}\left\langle \left. \Phi ^{+}\right| _{a b}\right. \, 1-\sum _{i=1}^{2} P_{i}^{C}\) | ||||
The tomographic scanning operator is
The Kraus operator is
While the key maps are
Appendix B: Channel model
In this section, we will provide a description of the channel model used in our simulation. The channels utilized in our simulation include loss, misalignment, and dark count rate channels, which are similar to [55].
1.1 1 BB84
In the WCP source, the output is a coherent state with amplitude of \(\mu \). After passing through the misaligned channel, the amplitude reaching each detector can be summarized as
Bob’s detectors (passive detection) | |||||
|---|---|---|---|---|---|
\(\mathrm {Z_{+}}\) | \(\mathrm {Z_{-}}\) | \(\mathrm {X_{+}}\) | \(\mathrm {X_{-}}\) | ||
\(\mathrm {Z_{+}}\) | \(\sqrt{p_{Z}} \cos \theta \) | \(\sqrt{p_{Z}} \sin \theta \) | \(\sqrt{p_{X}} \cos \alpha \) | \(\sqrt{p_{X}} \sin \alpha \quad \quad \qquad (B1)\) | |
Alice | \(\mathrm {Z_{-}}\) | \(-\sqrt{p_{Z}} \sin \theta \) | \(\sqrt{p_{Z}} \cos \theta \) | \(\sqrt{p_{X}} \sin \alpha \) | \(-\sqrt{p_{X}} \cos \alpha \) |
sends | \(\mathrm {X_{+}}\) | \(\sqrt{p_{Z}} \sin \alpha \) | \(\sqrt{p_{Z}} \cos \alpha \) | \(\sqrt{p_{X}} \cos \theta \) | \(-\sqrt{p_{X}} \sin \theta \) |
\(\mathrm {X_{-}}\) | \(\sqrt{p_{Z}} \cos \alpha \) | \(-\sqrt{p_{Z}} \sin \alpha \) | \(\sqrt{p_{X}} \sin \theta \) | \(\sqrt{p_{X}} \cos \theta \) | |
Here, \(\alpha =\frac{\pi }{4} -\theta \), \(\theta \) is the misalignment. Considering the channel loss, the loss factor \(\sqrt{\mu \eta } \) should be multiplied before the above amplitudes. By considering the dark count, we can get the click probability of each detector:
where \(\alpha _{j|i}\) is the amplitude reaching the detector, \(p_\textrm{d}\) is the detector dark count rate \(i,j\in \left\{ H,V,+,-\right\} \). The probabilities of individual detector clicks are known, for a given i, there could be a total of 4 detectors that will register a click, leading to 16 possible detection patterns. The probability of each detection pattern \( b_{1} b_{2} b_{3} b_{4} \) is represented by
where \(b_{k} \) represents the response of the k detectors, \(b_{k}=0,1 \). \(\overline{b_{k}} \) is the bit flip of \(\overline{b_{k}}\).
For a given signal intensities \(\mu \) (\(\mu \in \left\{ u, v, w \right\} \)), iterate through all the i and all of the detection mode to obtain \(4\times 16\) data, and then write it into a matrix \(P_{raw,\mu }\) with \(4\times 16\) data.
Suppose that double-click events on the same basis are randomly assigned to a measurement value, while double-click events on different basis are discarded. The following deletion model is defined:
Then the simulated statistical data can be given by
1.2 2 MDI
In the case of MDI, the WCP source of Alice and Bob transmits a weak coherent state with amplitude of \(\mu \). After passing through the misaligned channel, the signals of Alice and Bob are mismatched \(\theta _{A}\), \(\theta _{B}\). Because H and V are different modes, we can simply think of \(\sqrt{\mu _{A}} \cos \theta _{A} \) in H mode (similar to Alice and Bob), \(\sqrt{\mu _{A}} \sin \theta _{A} \) in mode V(Alice and Bob are similar); then, the amplitude reaching each detector is expressed as follows:
Then the click probability of each detector can be given by
where \(\alpha _{k \mid i j}^{\phi }\) is the amplitude reaching the detector, \(i,j\in \left\{ H,V,+,-\right\} \), \(k\in \left\{ 3\,H,3V,4\,H,4V\right\} \).
For fixed i, j, a total of 4 detectors may respond, which results in a total of 16 possible detection modes. The response probability of each detection mode \( b_{1} b_{2} b_{3} b_{4} \) is given by
where \(b_{k} \) represents the response of the k detectors, \(b_{k}=0,1 \). \(\overline{b_{k}} \) is the bit flip of \(\overline{b_{k}}\).
For a given signal intensities \(\mu _{A}\mu _{B}\) (\(\mu _{A},\mu _{B} \in \left\{ u, v, w \right\} \)), traverse all i, j and detection modes, there are \( 4\times 4\times 16\) data in total. Write the data as \(P_{raw,\mu _{A}\mu _{B}}\) and define the following deletion model
Then the simulated statistical data can be given by
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Li, Z., Zheng, B., Zhang, C. et al. Improved security bounds against the Trojan-horse attack in decoy-state quantum key distribution. Quantum Inf Process 23, 40 (2024). https://doi.org/10.1007/s11128-023-04238-0
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-023-04238-0