Abstract
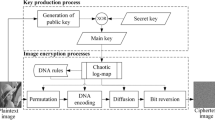
This paper proposes two attack methods to break the encryption algorithm using minimax differential evolution-based 7D hyper-chaotic map. In attack method 1, the secret keys generated by the 7D hyper-chaotic map can be directly revealed through two pairs of plain/cipher images. Once the secret keys are known, any cipher image can be decrypted easily. In attack method 2, we build three dictionary matrices of R, G and B channels firstly, and the corresponding plain image pixel value can be queried in the dictionary matrix one by one without using the secret keys or any system parameter. Experimental results demonstrate that the cryptosystem can be broken successfully by either of the proposed methods, thus avoiding the potential unexpected loss caused by the use of insecure encryption schemes.






Similar content being viewed by others
Data availability
All data included in this study are available upon request by contact with the corresponding author.
References
Azimi Z, Ahadpour S (2020) Color image encryption based on dna encoding and pair coupled chaotic maps. Multimed Tools Appl 79:1727–1744. https://doi.org/10.1007/s11042-019-08375-6
Chen T-H, Chang-Sian W (2010) Compression-unimpaired batch-image encryption combining vector quantization and index compression. Inf Sci 180(9):1690–1701. https://doi.org/10.1016/j.ins.2009.12.021
Fan H, Li M, Liu D, Zhang E (2017) Cryptanalysis of a colour image encryption using chaotic APFM nonlinear adaptive filter. Signal Process 143:28–41. https://doi.org/10.1016/j.sigpro.2017.08.018
Gaurav Bhatnagar QM, Jonathan W, Raman B (2013) Discrete fractional wavelet transform and its application to multiple encryption. Inf Sci 223:297–316. https://doi.org/10.1016/j.ins.2012.09.053
Ghadirli HM, Nodehi A, Enayatifar R (2019) An overview of encryption algorithms in color images. Signal Process 164:163–185. https://doi.org/10.1016/j.sigpro.2019.06.010
Girdhar A, Kumar V (2018) A RGB image encryption technique using Lorenz and Rossler chaotic system on DNA sequences. Multimed Tools Appl 77:27017–27039. https://doi.org/10.1007/s11042-018-5902-z
Hsiao H-I, Lee J (2015) Color image encryption using chaotic nonlinear adaptive filter. Signal Process 117:281–309. https://doi.org/10.1016/j.sigpro.2015.06.007
Hua Z, Zhou Y (2017) Design of image cipher using block-based scrambling and image filtering. Inf Sci 396:97–113. https://doi.org/10.1016/j.ins.2017.02.036
Kaur M, Kumar V (2018) An efficient image encryption method based on improved lorenz chaotic system. Electron Lett 54(9):562–564
Kaur M, Kumar V (2018) Adaptive differential evolution-based Lorenz chaotic system for image encryption. Arab J Sci Eng 43:8127–8144. https://doi.org/10.1007/s13369-018-3355-3
Kaur M, Singh D, Kumar V (2020) Color image encryption using minimax differential evolution-based 7d hyper-chaotic map. Appl Phys B Lasers Opt 126(9):1–19
Kerckhoffs’s principle (2020) http://www.crypto-it.net/eng/theory/kerckhoffs.html (last access on March, 29,2020)
Li C (2016) Cracking a hierarchical chaotic image encryption algorithm based on permutation. Signal Process 118:203–210. https://doi.org/10.1016/j.sigpro.2015.07.008
Li C, Lin D, Lu J (2017) Cryptanalyzing an image-scrambling encryption algorithm of pixel bits. IEEE Multimed 24(3):64–71
Li C, Lin D, Feng B, Lü J, Hao F (2018) Cryptanalysis of a chaotic image encryption algorithm based on information entropy. IEEE Access 6:75834–75842
Li M, Lu D, Xiang Y, Zhang Y, Ren H (2019) Cryptanalysis and improvement in a chaotic image cipher using two-round permutation and diffusion. Nonlin Dyn 96(1):31–47
Manjit K, Vijay K (2018) Color image encryption technique using differential evolution in nonsubsampled contourlet transform domain. IET Image Process 12(7):1273–1283
Qiu X, Xu J-X, Xu Y, Tan KC (2018) A new differential evolution algorithm for minimax optimization in robust design. IEEE Trans Cybern 48(5):1355–1368
Xu L, Li Z, Li J, Hua W (2016) A novel bit-level image encryption algorithm based on chaotic maps. Opt Lasers Eng 78:17–25. https://doi.org/10.1016/j.optlaseng.2015.09.007
Yap WS, Phan CW, Yau WC, Heng SH (2015) Cryptanalysis of a new image alternate encryption algorithm based on chaotic map. Nonlin Dyn 80(3):1483–1491
Ye G, Pan C, Huang X, Zhao Z, He J (2018) A chaotic image encryption algorithm based on information entropy. Int J Bifurcation Chaos 28(01):1850010. https://doi.org/10.1142/S0218127418500098
Yong Z, Ac A, Yt A, Jd A, Gw B (2020) Plaintext-related image encryption algorithm based on perceptron-like network. Inf Sci 526:180–202. https://doi.org/10.1016/j.ins.2020.03.054
Zhang E, Li F, Niu B, Wang Y (2017) Server-aided private set intersection based on reputation. Inf Sci 387:108–194. https://doi.org/10.1016/j.ins.2016.09.056
Zhou Y, Panetta K, Sos Agaian CL, Chen P (2012) Image encryption using P-Fibonacci transform and decomposition. Opt Commun 285(5):594–608. https://doi.org/10.1016/j.optcom.2011.11.044
Zhou Y, Panetta K, Agaian S, Chen CLP (2013) (n, k, p)-gray code for image systems. IEEE Trans Cybern 43(2):515–529
Yang, Qigui, Zhu, Daoyu, et al. (2018) A new 7D Hyperchaotic system with five positive Lyapunov exponents coined. Int J Bifurcation Chaos Appl Sci Eng 28(05) 1850057. https://doi.org/10.1142/S0218127418500578
Acknowledgements
This work was supported by the National Natural Science Foundation of China (61602158) and the Science and Technology Research Project of Henan Province (212102210413).
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declared that they have no conflict of interest to this work.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix A
Appendix A
Proposition
Suppose that x is an 8-bit unsigned integer, then
Proof
XOR is a binary bitwise operation. Suppose that the binary form of x and another number y are as follows:
where the subscript denotes the corresponding base. We know
where the i-th operation
On the other side, (255-x)10 = (11111111- x1x2x3x4x5x6x7x8)2, where the i-th operation
There is neither carry nor borrow after the corresponding position subtraction. Comparing Eqs. (57) and Eq. (58),we get
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Liu, Y., Li, M. & Fan, H. Cryptanalysis of a color image encryption using minimax differential evolution-based 7D hyper-chaotic map. Multimed Tools Appl 82, 44209–44225 (2023). https://doi.org/10.1007/s11042-023-15445-3
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-023-15445-3