Abstract
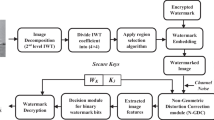
Watermarking is popular method for effective copyright protection of digital data. The invisible image watermarking is a type of watermarking which is used to conceal secret information in a cover image. In any watermarking system, there is a trade-off between imperceptibility and payload of the data to be hidden in the cover medium. Therefore, only a limited amount of data can be concealed in the cover image while watermark remain imperceptible. This paper proposes a new method of adaptive blind digital image data hiding in Discrete Cosine Transform (DCT) domain using Minimum Error Lease Significant Bit Replacement (MELSBR) method and Genetic Algorithm (GA). In the proposed method, the secret image is embedded into the DCT transformed cover image. Initially, the host and the secret image both are partitioned into equal sized blocks. Then for each secret image block, host image block is intelligently selected through GA and is embedded using MELSBR method. GA helps in identifying the target cover image blocks such that with the LSB embedding, both visual quality of the cover image and imperceptibility of the secret image remain least affected. In watermark extraction process, the watermarked image is decomposed into equal sized blocks and then using the Jigsaw Puzzle Solver (JPS) the secret image is reconstructed. In spite of doubling the payload of the data to hide, the experimental results have shown better imperceptibility and robustness results of the proposed method as compared to the current approaches in this domain.





Similar content being viewed by others
References
Anwar MJ, Ishtiaq M, Jaffar MA (2010) Block-based digital image watermarking using Genetic Algorithm, International Conference on Emerging Technologies (ICET), pp 204–209
Bender W, Morimoto N, Lu A (1996) Techniques for data hiding. IBM Syst J 35(3/4):313–336
Boland FM, Ruanaidh JJKO, Dautzenberg C (1995) Watermarking digital images for copyright protection, Proc. IEEE Conference on Image Processing and Its Applications, pp 326–331
Chan CK, Cheng LM (2004) Hiding data in images by simple LSB substitution. Pattern Recognit 37(3):469–474
Chan CK, Cheng LM, Leung KC, Li SL (2004) Image hiding based on block difference. Proceedings of the 8th International Conference on Control, Automation, Robotics and Vision (ICARCV 2004), Kuming, PRC, pp 968–972
Cox IJ, Kilian J, Leighton T, Shamoon T (1996) A Secure, robust watermark for multimedia, Workshop on Information Hiding, Newton Institute, Univ. of Cambridge
Ejaz N, Baik SW (2012) Video summarization using a network of radial basis functions. Multimedia Systems 18(6):483–497
Ejaz N, Mehmood I, Baik SW (2013) Efficient visual attention based framework for extracting key frames from videos. Signal Process Image Commun 28(1):34–44
Ejaz N, Tariq TB, Baik SW (2012) Adaptive key frame extraction for video summarization using an aggregation mechanism. J Vis Commun Image Represent 23(7):1031–1040
Findik O, Babaoglu I, Ulker E (2009) Watermarking scheme using an artificial immune system in spatial domain. Proceedings of the 2nd International conference on International sciences: Information Technology, Culture and Human, pp 945–950
Gen M, Cheng R (1997) Genetic algorithms and engineering design, John Wiley & Sons, Inc, New York
Ishtiaq M, Sikandar B, Jaffar MA (2010) Adaptive watermark strength selection using particle swarm optimization, ICIC Express Letters, An International journal of research and surveys
Khan UA (2010) BCH coding and intelligent watermark embedding: Employing both frequency and strength selection. Appl Soft Comput 10(1):332–343
Khan A, Mirza AM (2007) Genetic Perceptual shaping: utilizing cover image and conceivable attack information during watermark embedding. Inform Fusion 8(4):354–365
Lee YK, Chen LH (1999) An adaptive image steganographic model based on Minimum-Error LSB Replacement, Ninth National Conference on Information Security, Taichung, Taiwan, pp 8–15
Lee Y, Chen L (2000) High capacity image steganographic model. IEE Proc Vis Image Signal Proc 147(3):288–294
Li S, Leung K, Cheng LM, Chan C (2006) A novel image-hiding scheme based on block difference. Pattern Recognit 39(6):1168–1176
Michalewicz Z (1994) Genetic algorithms + data structure = evolution programs. Springer, Berlin
Piva A, Barni M, Bartolini F, Cappellini V (1997) DCT-based watermark recovering without resorting to the uncorrupted original image. Proc Int Conf Image Process 1:520–523
Radack GM, Badler NI (1982) Jigsaw puzzle matching using a boundary-centered polar encoding. Computer Graphics and Image Processing 19(1):1–17
Sikander B, Ishtiaq M, Jaffar MA, Tariq M, Mirza AM (2010) Adaptive digital watermarking of images using Genetic Algorithm, International Conference on Information Science and Applications (ICISA), pp 512–519, Seoul, Korea
Suganthan PN (1999) Solving jigsaw puzzles using Hopfield neural networks. Proceeding of International Joint Conference on Neural Networks, Washington D.C., pp 10–16
Tirkel A, Schyndel RV, Osborne C (1994) A Digital watermark. Proc ICIP 11:86–90
Wang RZ, Lin CF, Lin JC (2000) Hiding data in images by optimal moderately-significant-bit replacement. IEE Electron Lett 36(25):2069–2070
Wang RZ, Lin CF, Lin JC (2001) Image hiding by optimal LSB substitution and genetic algorithm. Pattern Recognit 34(3):671–683
Yao FH, Shao GF (2003) A shape and image merging technique to solve jigsaw puzzles. Pattern Recogn Lett 24(12):1819–1835
Zne-Jung L, Shih-Wei L, Shun-Feng S, Chun-Yen L (2008) A hybrid watermarking technique applied to digital images. Appl Soft Comput 8(1):798–808
Acknowledgment
This work was supported by the Industrial Strategic Technology Development Program (10041772, the Development of an Adaptive Mixed-Reality Space based on Interactive Architecture) funded by the Ministry of Knowledge Economy (MKE, Korea).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Ejaz, N., Anwar, J., Ishtiaq, M. et al. Adaptive image data hiding using transformation and error replacement. Multimed Tools Appl 73, 825–840 (2014). https://doi.org/10.1007/s11042-013-1377-0
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-013-1377-0