Abstract
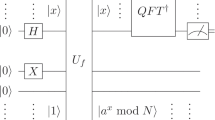
The fundamental security aspect of the classical crypto-system depends on integer factorization and discrete logarithm problems. The quantum factorization problem is a crucial problem in quantum computing as it has significant implications for cryptography and security. Shos’s paper on “Polynomial-time algorithms for discrete logarithms and factoring on a quantum compute” has become a threat to the classical crypto-system, influencing many researchers to work on factorization problems using quantum computing. Quantum Computers (QC) can be essential in running different factorization algorithms in polynomial time. However, practical implementation on larger numbers is still a major challenge due to the requirement for error correction and massive quantum devices. Although the quantum factorization issue puts traditional cryptographic systems at risk, it also opens up new possibilities for quantum communication and encryption. The challenge of factorization opens up an entirely new field for research into quantum communication protocol security, including quantum key distribution and the development of quantum-resistant cryptographic systems. This paper surveys the various quantum algorithms for factoring a number into prime integers. We present a simulation study of the Quantum factorization algorithm to determine the period of a process. Turning the factoring problem into the challenge of determining a function’s period is the essential strategy of practical implementation using the quantum circuit.


Similar content being viewed by others
Data availability
No data was generated during the research to disclose. No Code is available to share.
References
Shor PW. Polynomial time algorithms for discrete logarithms and factoring on a quantum computer. In: International algorithmic number theory symposium. Springer. 1994.
Pratama IPAE, Adhitya IGNAK. Post quantum cryptography: Comparison between rsa and mceliece. In: 2022 International Conference on ICT for Smart Society (ICISS). IEEE. 2022. p. 01–05.
Zhang K, Zhang J. A technique for designing nano-scale circuits using a fuzzy logic and nature-inspired fish swarm optimization algorithm. Optik. 2022;268:169756.
Knutsen H. A fractal uncertainty principle for the short-time Fourier transform and Gabor multipliers. Appl Comput Harmon Anal. 2023;62:365–89.
Bronzato JD, Bronzato JD, Brito AM, Bettini J, Passini MR, Gomes BP, Nantes IL. Degradation of ciprofloxacin by green cobalt oxide quantum dots. Appl Surf Sci. 2023;609:155193. https://doi.org/10.1016/j.apsusc.2022.155193.
Weinstein YS, Pravia MA, Fortunato EM, Lloyd S, Cory DG. Implementation of the quantum Fourier transform. Phys Rev Lett. 2001;86:1889–91. https://doi.org/10.1103/PhysRevLett.86.1889.
Suo J, Wang L, Yang S, Zheng W, Zhang J. Quantum algorithms for typical hard problems: a perspective of cryptanalysis. Quantum Inf Process. 2020;19(6):1–26.
Barrera P, Calabrò A, Fortuna L, Porto D. A new method for implementing gate operations in a quantum factoring algorithm. In: Proceedings of the 2003 International Symposium on Circuits and Systems, 2003. ISCAS’03. 2003;5:V–V. IEEE.
Nam Y, Su Y, Maslov D. Approximate quantum Fourier transform with O (n log (n)) T gates. NPJ Quantum Inf. 2020;6(1):26.
Burke JV, Lewis AS, Overton ML. The speed of Shor’s r-algorithm. IMA J Numer Anal. 2008;28(4):711–20.
Shepherd D, Bremner MJ. Temporally unstructured quantum computation. Proc R Soc A. 2009;465(2105):1413–39.
Aaronson S, Arkhipov A. The computational complexity of linear optics. In: Proceedings of the forty-third annual ACM symposium on theory of computing. 2011. p. 333–342
Hamdi SM, Zuhori ST, Mahmud F, Pal B. A compare between Shor’s quantum factoring algorithm and general number field sieve. In: 2014 International Conference on Electrical Engineering and Information & Communication Technology. IEEE. 2014. p. 1–6.
Hu Z, Liu S, Chen K. Privacy-preserving location-based services query scheme against quantum attacks. IEEE Trans Depend Secure Comput. 2018;17(5):972–83.
Fu X, Riesebos L, Rol M, Van Straten J, Van Someren J, Khammassi N, Ashraf I, Vermeulen R, Newsum V, Loh K, et al. eqasm: An executable quantum instruction set architecture. In: 2019 IEEE International Symposium on High Performance Computer Architecture (HPCA). IEEE. 2019. p. 224–237
de Avila AB, Reiser RH, Pilla ML, Yamin AC. State-of-the-art quantum computing simulators: Features, optimizations, and improvements for d-gm. Neurocomputing. 2020;393:223–33.
Lai H, Pieprzyk J, Pan L, Orgun MA. Two types of dynamic quantum state secret sharing based on tensor networks states. Physica A. 2021;582:126257.
Mousavi M, Houshmand M, Bolokian M. The cost reduction of distributed quantum factorization circuits. Int J Theoret Phys. 2021;60(4):1292–8.
Song HC, Liu XN, Jiang D, An J. Grover algorithm circuit optimization and noise analysis on integer factorization. In: 2022 7th International Conference on Intelligent Computing and Signal Processing (ICSP). IEEE. 2022. p. 101–107.
Kumar M. Post-quantum cryptography algorithms standardization and performance analysis. arXiv preprint arXiv:2204.02571. 2022.
Amaricci A, Crippa L, Scazzola A, Petocchi F, Mazza G, de Medici L, Capone M. Edipack: A parallel exact diagonalization package for quantum impurity problems. Comput Phys Commun. 2022;273:108261.
Zou P, Wang S, Gong X, Jiao JR, Zhou F. Quantum entanglement inspired hard constraint handling for operations engineering optimization with an application to airport shift planning. Expert Syst Appl. 2022;205: 117684.
Zidan M, Hegazy SF, Abdel-Aty M, Obayya SS. Rapid solution of logical equivalence problems by quantum computation algorithm. Appl Soft Comput. 2022;132: 109844.
Feng F, Zhang P, Zhou Y, Tang Z. Quantum microgrid state estimation. Electric Power Syst Res. 2022;212:108386.
Dey K, Debnath SK, Stănică P, Srivastava V. A post-quantum signcryption scheme using isogeny based cryptography. J Inf Secur Appl. 2022;69:103280.
Liu YP, Jia QS, Wang X. Quantum reinforcement learning method and application based on value function. IFAC-PapersOnLine. 2022;55(11):132–7.
Aaronson S, Chen L. Complexity-theoretic foundations of quantum supremacy experiments. arXiv preprint arXiv:1612.05903. 2016.
Bouland A, Fefferman B, Nirkhe C, Vazirani U. Quantum supremacy and the complexity of random circuit sampling. arXiv preprint arXiv:1803.04402. 2018.
Fouotsa TB, Petit C. Sims: a simplification of sigamal. In: International Conference on Post-Quantum Cryptography. Springer. 2021. p. 277–295.
Runge K, Hasan MA, Levine JA, Deymier PA. Demonstration of a two-bit controlled-not quantum-like gate using classical acoustic qubit-analogues. Sci Reports. 2022;12(1):1–6.
Willsch D, Willsch M, Jin F, De Raedt H, Michielsen K. Large-scale simulation of Shor’s quantum factoring algorithm. Mathematics. 2023;11(19):4222.
Skosana U, Tame M. Demonstration of Shor’s factoring algorithm for n= 21 on ibm quantum processors. Sci Reports. 2021;11(1):16599.
Grover LK. A fast quantum mechanical algorithm for database search. In: Proceedings of the twenty-eighth annual ACM symposium on theory of computing. 1996. p. 212–219.
Borges F, Reis PR, Pereira D. A comparison of security and its performance for key agreements in post-quantum cryptography. IEEE Access. 2020;8:142413–22.
Nguyen MH, Hoang CN, Moldovyan A, Moldovyan N, Vu HQ, Le Tran DK. A novel version of the hidden logarithm problem for post-quantum signature algorithms. Theoret Comput Sci. 2022;921:36–49.
Funding
The authors hereby declare that there was no full or partial financial support from any organization.
Author information
Authors and Affiliations
Contributions
Mandeep Kumar drafted the main manuscript text, Dr. Bhaskar Mondal prepared all the figures and did the proofreading and arranging the systematic review throughout. All authors equally contributed to the scientific work and reviewed the manuscript.
Corresponding authors
Ethics declarations
Conflict of interest
The authors do not have any financial or personal Conflict of interest to disclose related to this manuscript.
Ethical approval
No human and/ or animal studies have been presented in the manuscript. Hence, no ethical approval is needed.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This article is part of the topical collection “Security and Privacy 2020” guest edited by Pantelimon Stanica, Odelu Vanga and Sumit Kumar Debnath.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Kumar, M., Mondal, B. Study on Implementation of Shor’s Factorization Algorithm on Quantum Computer. SN COMPUT. SCI. 5, 413 (2024). https://doi.org/10.1007/s42979-024-02771-y
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s42979-024-02771-y