Abstract
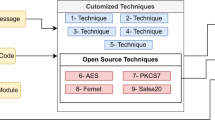
The previous secret image sharing schemes did not provide a copyright and privacy for cover images. The reason is that a dealer selects a cover image by itself and embeds directly the secret data into the cover image. In this paper, a reversible secret image sharing scheme in encrypted images is proposed in order to provide the copyright and privacy of the cover image. We divide a role of the dealer into an image provider and a data hider. The image provider encrypts the cover image and transmits the encrypted image to the data hider, and the standard stream cipher as one-time pad (OTP) with a random secret key is used. The data hider embeds the secret data into the encrypted image, and the encrypted shadow images are transmitted to the corresponding participant. We utilize the polynomial arithmetic operation over GF(28) during the sharing of the encrypted shadow images, and the coefficient of the highest-order term is fixed to one in order to prevent the overflow and the security problem. In the reconstruction procedure, the secret data can be extracted and the cover image can be reconstructed exactly from t or more encrypted shadow images with Lagrange interpolation. In experimental results, the proposed method shows that the PSNR is sustained close to 44 dB regardless of the embedding capacity, where the embedding capacity is 524,288 bits on average.









Similar content being viewed by others
References
Beimel A, Chor B (1998) Secret sharing with public reconstruction. IEEE Trans Inf Theory 44(5):1887–1896
Bender W, Gruhl D, Morimoto N, Lu A (1996) Techniques for data hiding. IBM Syst J 35(3.4):313–336
Berry S (1999) A simple publicly verifiable secret sharing scheme and its application to electronic voting. In: Advances in cryptology- CRYPTO’99. Lecture notes in computer science, vol 1666, pp 148–164
Chang C-C, Hsieh Y-P, Lin C-H (2008) Sharing secrets in stego images with authentication. J Pattern Recognit 41(10):3130–3137
Harn L, Fuyou M (2014) Multilevel threshold secret sharing based on the Chinese Remainder Theorem. Inf Process Lett 114(9):504–509
Hong W, Chen T-S, Wu H-Y (2012) An improved reversible data hiding in encrypted images using side match. IEEE Signal Process Lett 19(4):199–202
Josh B, Jerry L (1990) Generalized secret sharing and monotone functions. In: Advances in cryptology-CRYPTO’88. Lecture notes in computer science, LNCS, vol 403, pp 27–35
Katzenbeisser S, Petitcolas FAP (2000) Information Hidhing Techniques for steganography and digital watermarking. Artech House
Lin C-C, Liao LH, Hwang KF, Chen S-C (2012) Reversible secret-image sharing with high visual quality. Multimedia tools and applications. Springer, pp 1–19
Lin C-C, Tsai W-H (2004) Secret image sharing with steganography and authentication. J Syst Softw 73(3):405–414
Lin P-Y, Chan C-S (2010) Invertible secret image sharing with steganography. Pattern Recogn Lett 31(13):1887–1893
Luo L, Chen Z, Chen M, Zeng X, Xiong Z (2010) Reversible image watermarking using interpolation technique. IEEE Trans Inf Forensics Secur 5(1):187–193
Ma K-L, Zhang W, Zhao X, Yu N, Li F (2013) Reversible data hiding in encrypted images by reserving room before encryption. IEEE Trans Inf Forensics Secur 8(3):553–562
Martín del Rey A (2015) A multi-secret sharing scheme for 3D solid objects. Expert Syst Appl 42(4):2114–2120
Menezes AJ, Van Oorschot PC, Vanstone SA (1996) Handbook of applied cryptography. CRC Press
Mitsuru I, Akira S, Takao N (1989) Secret sharing scheme realizing general access structure. Electron Commun Jpn (Part III: Fundamental Electronic Science) 72(9):1520–6440
Mustafa U, Ulutas G, Nabiyev VV (2013) Invertible secret image sharing for gray level and dithered cover images. J Syst Softw 86(2):485–500
Naor M, Shamir A (1995) Visual cryptography. In: Advances in cryptology, EUROCRYPT’94. Springer, Berlin, Heidelberg
Naor M, Shamir A (1997) Visual cryptography II: improving the contrast via the cover base. Security protocols. Springer, Berlin
Pakniat N, Noroozi M, Eslami Z (2014) Secret image sharing scheme with hierarchical threshold access structure. J Vis Commun Image Represent 25(5):1093–1101
Paul F (1987) A practical scheme for Non-Interactive verifiable secret sharing. In: Proceedings of the 28th annual symposium on foundations of computer science, pp 427–438
Qin C, Chang C-C, Huang Y-H, Liao L-T (2013) An inpainting-assisted reversible steganographic scheme using a histogram shifting mechanism. IEEE Trans Circuits Syst Video Technol 23(7):1109–1118
Qin C, Zhang X (2015) Effective reversible data hiding in encrypted image with privacy protection for image content. J Vis Commun Image Represent 31:154–164
Shamir A (1979) How to share a secret. Commun. ACM 22:612–613
Stallings W (2006) Cryptography and network security, 4th edn. Prentice Hall
Stinson DR (2006) Cryptography theory and practice, 3rd edn. Chapman & Hall/CRC Press
Thien C-C, Lin J-C (2002) Secret image sharing. Comput Graph 26(5):765–770
Thien C-C, Lin J-C (2003) An image sharing method with user-friendly shadow images. IEEE Trans Circuits Syst Video Technol 13(12):1161–1169
Van Schyndel RG, Tirkel AZ, Osborne CF (1994) A digital watermark, vol 2. IEEE
Wang R-Z, Shyu S-J (2007) Scalable secret image sharing. J Signal Process Image Commun 22(4):363–373
Yang C-N, Chen T-S, Yu K-H, Wang C-C (2007) Improvements of image sharing with steganography and authentication. J Syst Softw 80(7):1070–1076
Yuan H-D (2014) Secret sharing with multi-cover adaptive steganography. Inf Sci 254:197–212
Zhang X (2011) Reversible data hiding in encrypted image. IEEE Signal Process Lett 18(4):255–258
Acknowledgments
This research was supported by Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Education(No. 2015R1D1A1A01058019).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Shin, SH., Jung, KH. Reversible secret image sharing scheme in encrypted images. Multimed Tools Appl 75, 13931–13949 (2016). https://doi.org/10.1007/s11042-016-3844-x
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-016-3844-x