Abstract
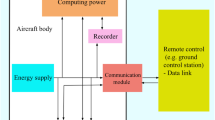
Drones are the recent advancements in defense applications as they can perform unmanned aerial surveys. The internet of drone (IoD) is an emerging concept in drone/node communication, which has evolved with the 5G-oriented networks. Due to the rapid usage of high-speed advanced computing systems and 5G networks, the user data are continuously updated and shared. Therefore, security/privacy is necessary between users and an efficient authentication approach using a robust security key. Existing techniques have several limitations while handling the attack sequences in data transmission over IoD environment systems. A novel elliptic curve cryptographic-based Chebyshev polynomial source authentication schema is proposed to enable secure data services between users to access information directly from one drone/node authorized access from other drone/user in 5G network systems. Also, we use elliptic curve cryptography for secure authentication to each node to share session key with a similar secure channel to transmit data with interactive computational complexity and secure communication in wireless IoD. The theoretical security-related analysis presented in this paper gives better insight into efficient, secure data transmission with increased quality of service parameters described in wireless IoD environment.






Similar content being viewed by others
Data Availablility
Not applicable.
References
Challa S, Wazid M, Das AK, Kumar N, Reddy AG, Yoon EJ, Yoo KY (2017) Secure signature-based authenticated key establishment scheme for future IoT applications. IEEE Access 5:3028–3043
Chatterjee S, Roy S, Das AK, Chattopadhyay S, Kumar N, Vasilakos AV (2016) Secure biometric-based authentication scheme using Chebyshev chaotic map for multi-server environment. IEEE Trans Depend Sec Comput. https://doi.org/10.1109/TDSC.2016.2616876
Chaudhry SA, Naqvi H, Mahmood K, Ahmad HF, Khan MK (2017) An improved remote user authentication Schemeusing elliptic curve cryptography. Wireless Pers Commun 96(4):5355–5373
Choi Y, Lee D, Kim J et al (2014) security enhanced user authentication protocol for wireless sensor networks using elliptic curves cryptography. Sensors 14(6):10081–10106
Das AK, Wazid M (2018) Design and analysis of secure lightweight remote user authentication and key agreement scheme in internet of drones deployment. IEEE Internet Things J 2327–4662. (c) 2018 IEEE. Personal use is permitted, but republication/redistribution requires IEEE permission
Doss R, Zhou W, Yu S (2013) Secure RFID tag ownership transfer based on quadratic residues. IEEE Trans Inf Forensics Secur 8(2):390401
Farash MS, Turkanovic M, Kumari S, Hölbl M (2016) An efficient ´user authentication and key agreement scheme for heterogeneous wireless sensor network tailored for the internet of things environment. Adhoc Netw 36:152–176
Gharibi M, Boutaba R, Waslander SL (2016) Internet of drones. IEEE Access 4:1148–1162
Hall RJ (2016) An internet of drones. IEEE Internet Comput 20(3):68–73
Irshad A, Ahmad HF, Alzahrani BA, Sher M, Chaudhry SA (2016) An efficient and anonymous chaotic map based authenticated key agreement for multi-server architecture. KSII Trans Internet Inf Syst 10(12):5572–5595
Jiang Q, Zeadally S, Ma J, He D (2017) Lightweight three-factor authentication and key agreement protocol for internet-integrated wireless sensor networks. IEEE Access 5:3376–3392
Koubaa A, Qureshi B, Sriti MF, Allouch A, Javed Y, Alajlan M, Cheikhrouhou O, Khalgui M, Tovar E (2019) Dronemap planner: a service-oriented cloud-based management system for the internet-ofdrones. Ad Hoc Netw 86:46–62
Lee J-H, Wazid M, Das AK (2018) Authentication protocols for the internet of drones: taxonomy, analysis and future directions. J Ambient Intell Humaniz Comput 2018:1–10
Li Y, Zhang Z (2018) User authentication protocol based on Chebyshev polynomial for wireless sensor networks. In: 2018 IEEE 3rd advanced information technology, electronic and automation control conference (IAEAC 2018)
Lin H-Y (2015) Improved chaotic maps-based password-authenticated key agreement using smart cards. Commun Nonlinear Sci Numer Simul 20(2):482–488
Lin C, He D, Kumar N, Choo KKR, Vinel A, Huang X (2018a) Security and privacy for the internet of drones: challenges and solutions. IEEE Commun Mag 56(1):64–69
Lin C, He D, Kumar N, Choo K-KR, Vinel A, Huang X (2018) Security and privacy for the internet of drones: challenges and solutions. IEEE Commun Mag 56(1):64–69
Motlagh NH, Taleb T, Arouk O (2016) Low-altitude unmanned aerial vehicles-based internet of things services: comprehensive survey and future perspectives. IEEE Internet Things J 3(6):899–922
Nagel H, Bondt G, Custers B (2016) Drone technology: types, payloads, applications, frequency spectrum issues and future developments. In: The future of drone use opportunities and threats from ethical and legal perspectives, vol. 27, chapter 2. Springer Gabler Verlag, pp 21–45
Odelu V, Das AK, Goswami A (2015) A secure biometrics-based multi-server authentication protocolusing smart cards. IEEE Trans Inf Forensics Secur 10(9):1953–1966
Roy S, Chatterjee S, Das AK, Chattopadhyay S, Kumari S, Jo M (2018) Chaotic map-based anonymous user authentication scheme with user biometrics and fuzzy extractor for crowdsourcing internet of things. IEEE Internet Things J 5(4):2884–2895
Seo S-H, Won J, Bertino E (2015) A secure communication protocol for drones and smart objects. In: Proceedings of the 10th ACM symposium on information, computer and communications security, pp 249–260
Srinivas J, Das AK, Kumar N, Rodrigues J (2018) Cloud centric authentication for wearable healthcare monitoring system. IEEE Trans Depend Sec Comput. https://doi.org/10.1109/TDSC.2018.2828306
Srinivas J, Das AK, Wazid M, Kumar N (2018a) Anonymous lightweight chaotic map-based authenticated key agreement protocol for industrial Internet of Things. IEEE Trans Depend Sec Comput 17:1133–1146
Srinivas J, Das AK, Kumar N, Rodrigues JJPC (2019) TCALAS: temporal credential-based anonymous lightweight authentication scheme for Internet of drones environment. IEEE Trans Veh Technol 68(7):6903–6916
Tran M-T, Duong A-D (2019) Improved Chebyshev polynomials-based authentication scheme in client-server environment. In: Hindawi security and communication networks, volume 2019, Article ID 4250743. https://doi.org/10.1155/2019/4250743.
Vergouw B, Nagel H, Bondt G, Custers B (2016) Drone technology: types, payloads, applications, frequency spectrum issues and future developments. T.M.C. Asser Press, The Hague, pp 21–45
Wang D, Cheng H, Wang P, Huang X, Jian G (2017) Zipf’s law in passwords. IEEE Trans Inf Forensics Secur 12(11):2776–2791
Wazid M, Das AK, Kumar N, Vasilakos AV, Rodrigues JJ (2018) Design and analysis of secure lightweight remote user authentication and key agreement scheme in Internet of drones deployment. IEEE Internet Things J. https://doi.org/10.1109/JIOT.2018.2888821
Wazid M, Das AK, Lee J-H (2018b) Authentication protocols forthe internet of drones: taxonomy, analysis and future directions. J Ambient Intell Humaniz Comput. https://doi.org/10.1007/s12652-018-1006-x
Wazid M, Das AK, Odelu V, Kumar N, Susilo W (2018) Secure remote user authenticated key establishment protocol for smart home environment. IEEE Trans Depend Secur Comput. https://doi.org/10.1109/TDSC.2017.2764083
Zhu H (2015) Cryptanalysis and improvement of a mobile dynamic ID authenticated key agreement scheme based on chaotic maps. Wireless Pers Commun 85(4):2141–2156
Funding
Not applicable.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Selvi, P.T., Sri, T.S., Rao, M.N. et al. Toward efficient security-based authentication for the internet of drones in defense wireless communication. Soft Comput 26, 4905–4913 (2022). https://doi.org/10.1007/s00500-021-06678-1
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00500-021-06678-1