Abstract
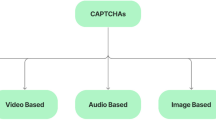
The ability to tell humans and computers apart is imperative to protect many services from misuse and abuse. For this purpose, tests called CAPTCHAs or HIPs have been designed and put into production. Recent history shows that most (if not all) can be broken given enough time and commercial interest: CAPTCHA design seems to be a much more difficult problem than previously thought. The assumption that difficult-AI problems can be easily converted into valid CAPTCHAs is misleading. There are also some extrinsic problems that do not help, especially the big number of in-house designs that are put into production without any prior public critique. In this paper we present a state-of-the-art survey of current HIPs, including proposals that are now into production. We classify them regarding their basic design ideas. We discuss current attacks as well as future attack paths, and we also present common errors in design, and how many implementation flaws can transform a not necessarily bad idea into a weak CAPTCHA. We present examples of these flaws, using specific well-known CAPTCHAs. In a more theoretical way, we discuss the threat model: confronted risks and countermeasures. Finally, we introduce and discuss some desirable properties that new HIPs should have, concluding with some proposals for future work, including methodologies for design, implementation and security assessment.
Chapter PDF
Similar content being viewed by others
References
Chow, R., Golle, P., Jakobsson, M., Wang, L., Wang, X.: Making CAPTCHAs Clickable. In: Proc. of HotMobile 2008 (2008)
Hernandez-Castro, C.J., Ribagorda, A.: VideoCAPTCHAs. In: Proceedings of the 5th International Conference on Security and Protection of Information, Brno (to be puslished, 2009)
Athanasopoulos, E., Antonatos, S.: Enhanced CAPTCHAs: Using Animation to Tell Humans and Computers Apart. In: IFIP International Federation for Information Processing (2006)
Bigham, J.P., Cavender, A.C.: Evaluating Existing Audio CAPTCHAs and an Interface Optimized for Non-Visual Use. In: CHI 2009 (2009)
Hernandez-Castro, C.J., Ribagorda, A., Saez, Y.: Side-channel attack on labeling CAPTCHAs (2009), http://arxiv.org/abs/0908.1185
Holmes, G., Donkin, A., Witten, I.H.: Weka: A machine learning workbench. In: Proceedings of the Second Australia and New Zealand Conference on Intelligent Information Systems, Brisbane, Australia (1994)
Quinlan, R.: Machine Learning. Morgan Kaufmann Pub., CA
Golle, P.: Machine Learning Attacks Against the Asirra CAPTCHA. In: ACM CCS 2008 (2008)
Hernandez-Castro, C.J., Ribagorda, A.: Preliminary analysis on the Megaupload CAPTCHA (Submitted for publication)
Achint, T., Venu, G.: Generation and Performance Evaluation of Synthetic Handwritten CAPTCHAs. In: ICFHR 2008 (2008)
Hernandez-Castro, C.J., Ribagorda, A.: Pitfalls in CAPTCHA design and implementation: the Math CAPTCHA, a case study (Submitted for publication)
Tam, J., Simsa, J., Hyde, S., Von Ahn, L.: Breaking Audio CAPTCHAs, http://www.captcha.net/Breaking_Audio_CAPTCHAs_OnlinePDF.pdf
von Ahn, L., Maurer, B., McMillen, C., Abraham, D., Blum, M.: reCAPTCHA: Human-Based Character Recognition via Web Security Measures. Science Magazine 321(5895), 1465–1468 (2008)
Caine, A., Hengartner, U.: The AI Hardness of CAPTCHAs does not imply Robust Network Security. In: IFIP, Trust Management, vol. 238, pp. 367–382
W3C Working Draft, Techniques for WCAG 2.0. G144: Ensuring Web Page contains another CAPTCHA serving same purpose using a different modality
Elson, J., Douceur, J.R., Howell, J., Saul, J.: Asirra: A CAPTCHA that Exploits Interest-Aligned Manual Image Categorization. In: Proccedings of the 14th ACM CCS (2007)
von Ahn, L., Blum, M., Hopper, N.J., Langford, J.: CAPTCHA: Using hard AI problems for security. In: Biham, E. (ed.) EUROCRYPT 2003. LNCS, vol. 2656, pp. 294–311. Springer, Heidelberg (2003)
Mori, G., Malik, J.: Recognizing objects in adversarial clutter: Breaking a visual CAPTCHA. In: Proc. of CVPR 2003, pp. 134–144. IEEE, Los Alamitos (2003)
Naor, M.: Verification of human in the loop or Identification via Turing Test, http://www.wisdom.weizmann.ac.il/~naor/PAPERS/human.ps (retrieved January 1, 2009)
Chew, M., Tygar, J.D.: Image recognition CAPTCHAs. In: Proc. of ISC 2004, pp. 268–279 (2004); A longer version as UC Berkeley Computer Science Division technical report UCB/CSD-04-1333
von Ahn, L., Dabbish, L.: Labeling Images with a Computer Game. In: ACM Conference on Human Factors in Computing Systems, CHI 2004, pp. 319–326 (2004)
US Patent no. 6,195,698, Method for selectively restricting access to computer systems, http://www.freepatentsonline.com/6195698.html
Rusu, A., Govindaraju, V.: Handwritten CAPTCHA: using the difference in the abilities of humans and machines in reading handwritten words. In: Proceedings of the IWFHR-9, Tokyo, Japan, pp. 226–231 (2004)
Stevanovic, R., et al.: Quantum Random Bit Generator Service for Monte Carlo and Other Stochastic Simulations. In: Lirkov, I., Margenov, S., Waśniewski, J. (eds.) LSSC 2007. LNCS, vol. 4818, pp. 508–515. Springer, Heidelberg (2008)
Baird, H.S., Riopka, T.: ScatterType: a Reading CAPTCHA Resistant to Segmentation Attack. In: Proc. of the IS & T/SPIE Document Recognition & Retrieval Conference, pp. 197–207 (2005)
Datta, R., et al.: IMAGINATION: A Robust Image-based CAPTCHA Generation System. In: Proc. of ACM Multimedia Conf., pp. 331–334 (2005)
Hoque, M.E., Russomanno, D.J., Yeasin, M.: 2D Captchas from 3D Models. In: Proceedings of the IEEE SoutheastCon 2006, Memphis (April 2006)
Chew, M., Baird, H.S.: BaffleText: a Human Interactive Proof. In: Proceedings of the 10th SPIE/IS&T Doc. Recog. Retr. Conf, DRR 2003 (2003)
Baird, H.S., Bentley, J.L.: Implicit CAPTCHAs. In: Proc. SPIE/IS&T Conf. on Document Recognition and Retrieval XII (DR & R 2005), pp. 191–196 (2005)
Moy, G., et al.: Distortion Estimation Techniques in Solving Visual CAPTCHAs. In: Proc. of the CVPR 2004, vol. 2 (2004)
Yan, J., Ahmad, A.S.E.: Breaking Visual CAPTCHAs with Naive Pattern Recognition Algorithms. In: Proceedings of the ACSAC 2007 (2007)
Chellapilla, K., Simard, P.Y.: Using Machine Learning to Break Visual HIPs. In: Proc. of the Conf. on Neural Information Processing Systems, NIPS 2004 (2004)
Chellapilla, K., Larson, K., Simard, P.Y., Czerwinski, M.: Computers beat Humans at Single Character Recognition in Reading based Human Interaction Proofs (HIPs). In: Procs. of CEAS (2005)
Hernandez-Castro, C.J., Ribagorda, A.: Analysis of the Teabag CAPTCHA version 1.2 (Submitted for publication)
DarkSEO programming: letter derotation, http://www.darkseoprogramming.com/2008/04/05/letter-derotation/
PWNtcha, http://caca.zoy.org/wiki/PWNtcha
TROJ_CAPTCHAR.A Trojan horse to relay CAPTCHAs at TrendMicro, http://blog.trendmicro.com/captcha-wish-your-girlfriend-was-hot-like-me/
Danchev, D.: Inside India’s CAPTCHA solving economy, http://blogs.zdnet.com/security/?p=1835
Van der Vorm, J.: Defeating audio (voice) CATPCHAs, http://vorm.net/captchas
Santamarta, R.: Breaking GMail’s audio CAPTCHA, http://blog.wintercore.com/?p=11
Kittenauth, O.W.: http://www.thepcspy.com/kittenauth
Techworld.com article on fallen CAPTCHAS, http://www.techworld.com/security/features/index.cfm?featureid=4168
Hernandez-Castro, C.J., Ribagorda, A.: Pitfalls in CAPTCHA design and implementation: the Math CAPTCHA, a case study. Computers & Security (2009), http://dx.doi.org/10.1016/j.cose.2009.06.006
Yeen, H.: Breaking CAPTCHAs without using OCR, http://www.puremango.co.uk/2005/11/breaking_captcha_115/
W. Wieser. Captcha recognition via averaging, http://www.triplespark.net/misc/captcha/
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 IFIP International Federation for Information Processing
About this paper
Cite this paper
Hernandez-Castro, C.J., Ribagorda, A. (2009). Remotely Telling Humans and Computers Apart: An Unsolved Problem. In: Camenisch, J., Kesdogan, D. (eds) iNetSec 2009 – Open Research Problems in Network Security. 2009. IFIP Advances in Information and Communication Technology, vol 309. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-05437-2_2
Download citation
DOI: https://doi.org/10.1007/978-3-642-05437-2_2
Published:
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-05436-5
Online ISBN: 978-3-642-05437-2
eBook Packages: Computer ScienceComputer Science (R0)