Abstract
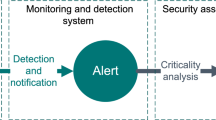
The investigation of the effectiveness of alert correlation methods implemented in the Alert Correlation Module was presented in the paper. The module was developed within the POSITIF project (Policy-based Security Tools and Framework) funded by the European Commission. Three effectiveness metrics were applied: reduction coefficient average ancestor count in alert trees and percentage of meta-alerts in outgoing alerts. Research was conducted using a test environment comprising 14 computers with IDS installed. Network traffic was monitored for 40 days, and during this time the IDSs generated 211 251 alerts. The module correlated and recognized as dangerous 6994 of them therefore achieving a level of reduction equal to 96.69 percent, which could be regarded as a good results.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Cuppens, F., Miege, A.: Alert Correlation in a Cooperative Intrusion Detection Framework. In: Proceedings of the 2002 IEEE Symposium on Security and Privacy, pp. 202–215. IEEE Computer Society Press, Los Alamitos (2002)
Danyliv, R., Meijer, J., Demchenko, Y.: The Incident Object Description Exchange Format (2006), http://www.ietf.org/internet-drafts/draft-ietf-inch-iodef-10.txt
Debar, H., Curry, D., Feinstein, B.: The Intrusion Detection Message Exchange Format (2006), http://tools.ietf.org/html/draft-ietf-idwg-idmef-xml-15
Debar, H., Wespi, A.: Aggregation and Correlation of Intrusion-Detection Alerts. In: Lee, W., Mé, L., Wespi, A. (eds.) RAID 2001. LNCS, vol. 2212, pp. 85–103. Springer, Heidelberg (2001)
Dörges, T., Kossakowski, K.P.: Proactive Security Monitoring in a Policy Managed Network. In: 18th Annual FIRST Conference (2006)
Lioy, A.: Positif (Policy-based Security Tools and Framework)—Annex (2003)
POSITIF Project Website (2003), http://www.positif.org
Prelude-IDS Project Websites. http://www.prelude-ids.org
Rose, M.: The Blocks Extensible Exchange Protocol Core (2001), http://www.rfc-editor.org/rfc/rfc3080.txt
Valdes, A., Skinner, K.: Probabilistic Alert Correlation. In: Lee, W., Mé, L., Wespi, A. (eds.) RAID 2001. LNCS, vol 2212, pp. 54–68. Springer, Heidelberg (2001)
Valeur, F., Vigna, G., Kruegel, C., Kemmerer, R.A.: A comprehensive approach to intrusion detection alert correlation. IEEE Transactions On Dependable and Secure Computing 1(3), 146–169 (2004)
Xu, D., Ning, P.: Alert Correlation through Triggering Events and Common Resources. In: Yew, P.-C., Xue, J. (eds.) ACSAC 2004. LNCS, vol. 3189, pp. 360–369. Springer, Heidelberg (2004)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Balcerek, B., Dragan, P., Trawinski, B., Wojtkicwicz, M. (2007). Investigation of the Effectiveness of Alert Correlation Methods in a Policy-Based Security Framework. In: Gorodetsky, V., Kotenko, I., Skormin, V.A. (eds) Computer Network Security. MMM-ACNS 2007. Communications in Computer and Information Science, vol 1. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-73986-9_28
Download citation
DOI: https://doi.org/10.1007/978-3-540-73986-9_28
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-73985-2
Online ISBN: 978-3-540-73986-9
eBook Packages: Computer ScienceComputer Science (R0)