Abstract
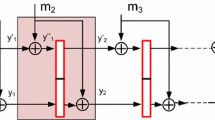
The security of hash functions has recently become one of the hottest topics in the design and analysis of cryptographic primitives. Since almost all the hash functions used today (including the MD and SHA families) have an iterated design, it is important to study the general security properties of such functions. At Crypto 2004 Joux showed that in any iterated hash function it is relatively easy to find exponential sized multicollisions, and thus the concatenation of several hash functions does not increase their security. However, in his proof it was essential that each message block is used at most once. In 2005 Nandi and Stinson extended the technique to handle iterated hash functions in which each message block is used at most twice. In this paper we consider the general case and prove that even if we allow each iterated hash function to scan the input multiple times in an arbitrary expanded order, their concatenation is not stronger than a single function. Finally, we extend the result to tree-based hash functions with arbitrary tree structures.
Chapter PDF
Similar content being viewed by others
References
Biham, E., Chen, R., Joux, A., Carribault, P., Lemuet, C., Jalby, W.: Collisions of SHA-0 and reduced SHA-1. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 36–57. Springer, Heidelberg (2005)
Daemen, J., Govaerts, R., Vandewalle, J.: A Framework for the Design of One-Way Hash Functions Including Cryptanalysis of Damgrd’s One-Way Function Based on a Cellular Automaton. In: Asiacrypt 1991 (1991)
De Santis, A., Yung, M.: On the Design of Provably Secure Cryptographic Hash. In: Damgård, I.B. (ed.) EUROCRYPT 1990. LNCS, vol. 473, pp. 412–431. Springer, Heidelberg (1991)
Gilbert, H., Handschuh, H.: Security Analysis of SHA-256 and Sisters, Selected Areas in Cryptography 2003 NIST Cryptographic Hash Workshop 2005 (2005)
Joux, A.: Multicollisions in Iterated Hash Functions. In: Franklin, M. (ed.) CRYPTO 2004. LNCS, vol. 3152, pp. 306–316. Springer, Heidelberg (2004)
Jutla, C., Patthak, A.: A Simple and Provably Good Code for SHA Message Expansion, IACR preprint archive
Kelsey, J., Schneier, B.: Second Preimages on n-bit Hash Functions for Much Less than 2n Work. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 474–490. Springer, Heidelberg (2005)
Kelsey, J., Kohno, T.: Herding Hash Functions and the Nostradamus Attack. In: NIST Cryptographic Hash Workshop 2005 (2005)
Lucks, S.: Design Principles for Iterated Hash Functions IACR preprint archive
Nandi, M., Stinson, D.R.: Multicollision Attacks on a Class of Hash Functions, IACR preprint archive
Preneel, B.: Analysis and design of cryptographic hash functions, PhD thesis, Katholieke Universiteit Leuven, Belgium (1993)
Preneel, B., Govaerts, R., Vandewalle, J.: Hash Functions Based on Block Ciphers: A Synthetic Approach. In: Stinson, D.R. (ed.) CRYPTO 1993. LNCS, vol. 773, pp. 368–378. Springer, Heidelberg (1994)
Preneel, B.: Design Principles for Dedicated Hash Functions. In: Anderson, R. (ed.) FSE 1993. LNCS, vol. 809, pp. 71–82. Springer, Heidelberg (1994)
Rivest, R., Shamir, A.: PayWord and MicroMint: Two simple micropayment schemes. In: CryptoBytes, vol. 2(1)
Rogaway, P., Shrimpton, T.: Cryptographic Hash-Function Basics: Definitions, Implications, and Separations for Preimage Resistance, Second-Preimage Resistance, and Collision Resistance, Fast Software Encryption 2004 (2004)
Wang, X., Lai, X., Feng, D., Chen, H., Yu, X.: Cryptanalysis of the Hash Functions MD4 and RIPEMD. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 1–18. Springer, Heidelberg (2005)
Wang, X., Yu, H., Yin, Y.: Efficient Collision Search Attacks on SHA-0. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 1–16. Springer, Heidelberg (2005)
Wang, X., Yin, Y., Yu, H.: Finding Collisions in the Full SHA-1 Collision Search Attacks on SHA1. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 17–36. Springer, Heidelberg (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Hoch, J.J., Shamir, A. (2006). Breaking the ICE – Finding Multicollisions in Iterated Concatenated and Expanded (ICE) Hash Functions. In: Robshaw, M. (eds) Fast Software Encryption. FSE 2006. Lecture Notes in Computer Science, vol 4047. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11799313_12
Download citation
DOI: https://doi.org/10.1007/11799313_12
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-36597-6
Online ISBN: 978-3-540-36598-3
eBook Packages: Computer ScienceComputer Science (R0)