Abstract
With the increasing number of hostile network attacks, anomaly detection for network security has become an urgent task. As there have not been highly effective solutions for automatic intrusion detection, especially for detecting newly emerging attacks, network traffic visualization has become a promising technique for assisting network administrators to monitor network traffic and detect abnormal behaviors.
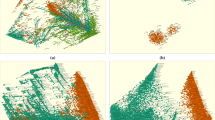
In this paper we present VisFlowCluster-IP, a powerful tool for visualizing network traffic flows using network logs. It models the network as a graph by modeling hosts as graph nodes. It utilizes the force model to arrange graph nodes on a two-dimensional space, so that groups of related nodes can be visually clustered in a manner apparent to human eyes. We also propose an automated method for finding clusters of closely connected hosts in the visualization space. We present three real cases that validate the effectiveness of VisFlowCluster-IP in identifying abnormal behaviors.
This research was supported in part by a grant from the Office of Naval Research (ONR) under the auspices of the National center for Advanced Secure Systems Research (NCASSR) <http://www.ncassr.org>.
Chapter PDF
Similar content being viewed by others
Keywords
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
References
S. Axelsson. Visualisation for Intrusion Detection-Hooking the Worm. Eighth European Symposium on Research in Computer Security (ESORICS), Lecture Notes in Computer Science (LNCS) 2808, Springer, 2003.
R. Ball, G. A. Fink, C. North. Home-Centric Visualization of Network Traffic for Security Administration. ACM CCS Workshop on Visualization and Data Mining for Computer Security (VizSEC/DMSEC), 2004.
R. Becker, S. Eick, A. Wilks. Visualizing network data. IEEE Transactions on Visualization and Computer Graphics, 1(1):16–28, 1995.
G. Conti, K. Abdullah. Passive Visual Fingerprinting of Network Attack Tools. ACM CCS Workshop on Visualization and Data Mining for Computer Security (VizSEC/DMSEC), 2004.
K. Cox, S. Eick, T. He. 3D Geographic Network Displays. ACMSIGMOD Record, 25(4):50–54, 1996.
F. Cuppens, A. Miege. Alert Correlation in a Cooperative Intrusion Detection Framework. IEEE Symp. on Security and Privacy, 2002.
H. Debar, A. Wespi. Aggregation and Correlation of Intrusion Detection Alerts. Int’l. Symp. on Recent Advances in Intrusion Detection (RAID), 2001.
M. Dodge, R. Kitchin. Atlas of Cyberspace. Addison-Wesley, 2001.
P. Eades. A Heuristic for Graph-Drawing. Congressus Numerantium, Vol 42, pp 149–160, 1984.
S. Eick, G. Wills. Navigating Large Networks with Hierarchies. IEEE Visualization, 1993.
R. Erbacher, K. Walker, D. Frincke. Intrusion and Misuse Detection in Large-Scale Systems. IEEE Comp. Graphics and Applications, 22(1):38–48, 2002.
M. Ester, H.-P. Kriegel, J. Sander, X. Xu. A Density-Based Algorithm for Discovering Clusters in Large Spatial Databases with Noise. ACM Int’l. Conf. on Knowledge Discovery and Data Mining (KDD), 1996.
T. Fruchterman, E. Reingold. Graph-Drawing by Force-Directed Placement. Software-Practice and Experience, Vol 21, pp 1129–1164, 1991.
C. Krugel, T. Toth, C. Keren Decentralized Event Correlation for Intrusion Detection. Int’l. Conf. on Info. Sec. and Cryptology (ICISC), 2001.
C. Krugel, T. Toth, E. Kirda. Service Specific Anomaly Detection for Network Intrusion Detection. ACM Symp. on Applied Computing, 2002.
K. Lakkaraju, W. Yurcik, A. J. Lee, R. Bearavolu, Y. Li, X. Yin. NVisionIP: NetFlow Visualizations of System State for Security Situational Awareness” ACM CCS Workshop on Visualization and Data Mining for Computer Security (VizSEC/DMSEC), 2004.
W. Lee, D. Xiang. Information-Theoretic Measures for Anomaly Detection. IEEE Symp. on Security and Privacy, 2001.
W. Lee, S. J. Stolfo, K. W. Mok. A Data Mining Framework for Building Intrusion Detection Models. IEEE Symp. on Security and Privacy, 1999.
A. Noack. An Energy Model for Visual Graph Clustering. Graph Drawing, 2003.
S. T. Teoh et al. Elisha: a Visual-based Anomaly Detection System. Int’l. Symp. on Recent Advances in Intrusion Detection (RAID), 2002.
S. T. Teoh, K. Ma, S. F. Wu. A Visual Exploration Process for the Analysis of Internet Routing Data. IEEE Visualization, 2003.
S. T. Teoh, K. Ma, S. F. Wu, X. Zhao. Case Study: Internet Visualization for Internet Security. IEEE Visualization, 2002.
J. Tölle, O. Niggemann. Supporting Intrusion Detection by Graph Clustering and Graph Drawing. Int’l. Symp. on Recent Advances in Intrusion Detection (RAID), 2000.
F. van Ham, J. J. van Wijk. Interactive Visualization of Small World Graphs. IEEE Info Vis, 2004.
X. Yin, W. Yurcik, A. Slagell. The Design of VisFlowConnect-IP: a Link Analysis System for IP Security Situational Awareness. IEEE Int’l. Workshop on Information Assurance (IWIA), 2005.
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 International Federation for Information Processing
About this paper
Cite this paper
Yin, X., Yurcik, W., Slagell, A. (2006). VisFlowCluster-IP: Connectivity-Based Visual Clustering of Network Hosts. In: Fischer-Hübner, S., Rannenberg, K., Yngström, L., Lindskog, S. (eds) Security and Privacy in Dynamic Environments. SEC 2006. IFIP International Federation for Information Processing, vol 201. Springer, Boston, MA. https://doi.org/10.1007/0-387-33406-8_24
Download citation
DOI: https://doi.org/10.1007/0-387-33406-8_24
Publisher Name: Springer, Boston, MA
Print ISBN: 978-0-387-33405-9
Online ISBN: 978-0-387-33406-6
eBook Packages: Computer ScienceComputer Science (R0)