Abstract
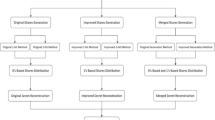
Secret sharing is an approach for accessing sensitive information by several authorized participants. It shares the secret key in different forms among several authorized participants, where a certain number of which is required to retrieve the original secret. This secret sharing raised a new practicality challenge of human secrecy memorization as well as limited number of users allowed, which have been addressed within this work. This paper examines two particular secret sharing techniques known as the counting-based secret sharing and the matrix-based secret sharing, which enhances the former to accommodate a high number of participants. This work aimed to serve participants accommodating the share’s memorization challenge via image steganography as well as testing both schemes in the cases of original 1-bit and 2-bit methods. We compared practicality applying the secret sharing methods combined with two image steganography methods: the least significant bit and the discrete wavelet transform. Our findings included interesting remarks regarding both security and robustness. Our results demonstrated that despite the large number of shares generated, as to serve more participants using the matrix-based scheme, its performance was highly satisfactory. Our experiments illustrated high imperceptibility levels for the matrix-based scheme, which in turn provides higher security and robustness compared to the original method, which provided very few shares serving a limited number of participants.













Similar content being viewed by others
References
Kini, N.; Kini, V.; Gautam: A Secured Steganography Algorithm for Hiding an Image in an Image. Studies in Computational Intelligence, Vol. 771, p. 539–546. Springer (2019)
Ogata, W.; Kurosawa, K.; Stinson, D.R.: Optimum secret sharing scheme secure against cheating. SIAM J. Discret. Math. 20(1), 79–95 (2006). https://doi.org/10.1137/S0895480100378689
Shamir, A.: How to share a secret. Commun. ACM 22(11), 612–613 (1979). https://doi.org/10.1145/359168.359176
Gutub, A.; Al-Juaid, N.; Khan, E.: Counting-based secret sharing technique for multimedia applications. Multimed. Tools Appl. 78(5), 5591–5619 (2019). https://doi.org/10.1007/s11042-017-5293-6
Porwal, S., Mittal, S.: A threshold secret sharing technique based on matrix manipulation. In: AIP Conference on Proceedings, 2214 (2020). https://doi.org/10.1063/5.0003358
Kadhim, I.J.; Premaratne, P.; Vial, P.J.; Halloran, B.: Comprehensive survey of image steganography: techniques, evaluations, and trends in future research. Neurocomputing 335, 299–326 (2019). https://doi.org/10.1016/j.neucom.2018.06.075
Hussain, M.; Wahab, A.W.A.; Bin Idris, Y.I.; Ho, A.T.S.; Jung, K.H.: Image steganography in spatial domain: a survey, signal process. Image Commun. 65, 46–66 (2018). https://doi.org/10.1016/j.image.2018.03.012
Bhargava, S.; Mukhija, M.: Hide image and text using LSB DWT and RSA based on image steganography ICTACT. J. Image Video Process 9(3), 1940–1946 (2019). https://doi.org/10.21917/ijivp.2019.0275
Yahya, A.: Steganography techniques. Steganogr. Tech. Digit. Images 2, 9–42 (2019). https://doi.org/10.1007/978-3-319-78597-4_2
Hamid, N.; Yahya, A.; Ahmad, R.B.; Al-Qershi, O.M.: Image steganography techniques: an overview. Int. J. Comput. Sci. Secur. 6(3), 168–187 (2012)
Kumar, V.; Kumar, D.: Performance evaluation of DWT based image steganography. IEEE 2nd Int. Adv. Comput. Conf. (IACC) (2010). https://doi.org/10.1109/IADCC.2010.5423005
Hamid, N., Yahya, A., Ahmad, R.B., Najim, L., Perlis, K.K.: Steganography in image files : a survey School of Computer and Communication Engineering University Malaysia Perlis (UniMAP) Ministry of Science and Technology Iraq, Baghdad 7(1), 35–55 (2013)
Shejul, A.A.; Kulkarni, U.L.: A DWT based approach for steganography using biometrics. DSDE—Int Conf. Data Storage Data Eng. 2010, 39–43 (2010). https://doi.org/10.1109/DSDE.2010.10
Alshoura, W.; Zainol, Z.; Teh, J.; Alawida, M.; Alabdulatif, A.: Hybrid SVD-based image watermarking schemes: a review. IEEE Access 9, 32931–32968 (2021). https://doi.org/10.1109/ACCESS.2021.3060861
Gutub, A.; Al-Shaarani, F.: Efficient Implementation of multi-image secret hiding based on LSB and DWT steganography comparisons. Arab. J. Sci. Eng. 45(4), 2631–2644 (2020). https://doi.org/10.1007/s13369-020-04413-w
Elharrouss, O.; Almaadeed, N.; Al-Maadeed, S.: An image steganography approach based on k-least significant bits (k-LSB). IEEE Int. Conf. Inform. IoT Enab. Technol. (ICIoT) (2020). https://doi.org/10.1109/ICIoT48696.2020.9089566
Sahu, A.K.; Swain, G.: A novel n-rightmost bit replacement image steganography technique. 3D Res. (2019). https://doi.org/10.1007/s13319-018-0211-x
Blakley G.: Safeguarding cryptographic keys. Int. Work. Manag. Req. Knowl., MARK (1979). https://doi.org/10.1109/MARK.1979.8817296
Miranda-López, V., et al.: Experimental analysis of secret sharing schemes for cloud storage based on RNS. Commun. Comput. Inf. Sci. 796, 370–383 (2018). https://doi.org/10.1007/978-3-319-73353-1_26
Tchernykh, A., et al.: Performance evaluation of secret sharing schemes with data recovery in secured and reliable heterogeneous multi-cloud storage. Cluster Comput. 22(4), 1173–1185 (2019). https://doi.org/10.1007/s10586-018-02896-9
Raman, R., Varshney, L.: Distributed storage meets secret sharing on the blockchain. Inf. Theory Appl. Workshop (ITA). https://doi.org/10.1109/ITA.2018.8503089
Fukumitsu, M., Hasegawa, S., Iwazaki, J., Sakai, M., Takahashi, D.: A proposal of a secure P2P-type storage scheme by using the secret sharing and the blockchain. In: International Conference on Advanced Information Networking and Applications, AINA, 2017, pp. 803–810. https://doi.org/10.1109/AINA.2017.11
Xiong, F.; Xiao, R.; Ren, W.; Zheng, R.; Jiang, J.: A key protection scheme based on secret sharing for blockchain-based construction supply chain system. IEEE Access 7, 126773–126786 (2019). https://doi.org/10.1109/ACCESS.2019.2937917
Rashid Ibrahim, D., Sen Teh, J., Abdullah, R., Ibrahim, D.R., Teh, J.S., Abdullah, R., Multifactor authentication system based on color visual cryptography, facial recognition and dragonfly optimization ARTICLE multifactor authentication system based on color visual cryptography, facial recognition and dragonfly optimization. Artic. Inf. Secur. J. A Glob. Perspect. 30(3): 149–159 (2020). https://doi.org/10.1080/19393555.2020.1817633
Al-Ghamdi, M.; Al-Ghamdi, M.; Gutub, A.: Security enhancement of shares generation process for multimedia counting-based secret-sharing technique. Multimed. Tools Appl. 78(12), 16283–16310 (2019). https://doi.org/10.1007/s11042-018-6977-2
Gutub, A.; Al-Qurashi, A.: Secure shares generation via m-blocks partitioning for counting-based secret sharing. J Eng Res 8(3), 91–117 (2020). https://doi.org/10.36909/JER.V8I3.8079
Al-Qurashi, A.; Gutub, A.: Reliable Secret key generation for counting-based secret sharing. J. Comput. Sci. Comput. Math. (JCSCM) 8(4), 87–101 (2018). https://doi.org/10.20967/jcscm.2018.04.006
Gutub, A.; Alkhodaidi, T.: Smart Expansion of Target Key for More Handlers to Access Multimedia Counting-Based Secret Sharing, Multimedia Tools and Applications (MTAP) (2020) (in press). https://doi.org/10.1007/s11042-020-08695-y
Gutub, A.; Al-Ghamdi, M.: Image based steganography to facilitate improving counting-based secret sharing, 3D research, Springer, ISSN 2092–6731, 10, 6 (2019). https://doi.org/10.1007/s13319-019-0216-0
Gutub, A.: Regulating watermarking semi-authentication of multimedia audio via counting-based secret sharing, Pamukkale University Journal of Engineering Sciences, in press (2021). https://doi.org/10.5505/pajes.2021.54837
Gutub, A.: Watermarking images via counting-based secret-sharing for lightweight semi-complete authentication. Int. J. Inf. Secur. Privacy (IJISP), Accepted in 2021, in press to appear in Vol. 16, No. 1, Aricle 18
Gutub, A.; Alaseri, K.: Refining Arabic text stego-techniques for shares memorization of counting-based secret sharing. J. King Saud Univ. Comput. Inf. Sci. (2019). https://doi.org/10.1016/j.jksuci.2019.06.014
AlKhodaidi, T.; Gutub, A.: Refining image steganography distribution for higher security multimedia counting-based secret-sharing, Multimed. Tools Appl. (MTAP), in press (2020). https://doi.org/10.1007/s11042-020-09720-w
Gutub, A.; Al-Ghamdi, M.: Hiding shares by multimedia image steganography for optimized counting-based secret sharing. Multimed. Tools Appl. (MTAP) 79, 7951–7985 (2020). https://doi.org/10.1007/s11042-019-08427-x
Kaggle: Dataset. https://www.kaggle.com/vic006/beginner. Accessed 30 Jan 2021
Pradhan, A.; Sahu, A.K.; Swain, G.; Sekhar, K.R.: Performance evaluation parameters of image steganography techniques. In: International Conference on Research Advances in Integrated Navigation Systems, RAINS 2016, pp. 1–8 (2016). https://doi.org/10.1109/RAINS.2016.7764399
Setiadi, D.: PSNR versus SSIM: imperceptibility quality assessment for image steganography. Multimed, Tools Appl, (2020). https://doi.org/10.1007/s11042-020-10035-z
Al-Shaarani, F.; Gutub, A.: Securing Matrix counting-based secret-sharing involving crypto steganography. J. King Saud University - Comput. Inform. Sci. (2021). https://doi.org/10.1016/j.jksuci.2021.09.009
Gutub, A.: Regulating watermarking semi-authentication of multimedia audio via counting-based secret sharing. Pamukkale University J. Eng. Sci. (2021). https://doi.org/10.5505/pajes.2021.54837
Shambour, M.K.; Gutub, A.: Personal privacy evaluation of smart devices applications serving hajj and umrah rituals. J. Eng. Res. (2021). https://doi.org/10.36909/jer.13199
Gutub, A.; Al-Roithy, B.: Varying PRNG to improve image cryptography implementation. J. Eng. Res. 9(3A), 153–183 (2021). https://doi.org/10.36909/jer.v9i3A.10111
Acknowledgements
Thanks are due to Umm Al-Qura University for motivating this collaborative research.
Funding
There is no funding source.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The authors declare that they have no conflict of interest.
Ethical Approval
This article does not contain any studies with human participants or animals performed by any of the authors.
Informed Consent
Informed consent was obtained from all individual participants included in the study.
Rights and permissions
About this article
Cite this article
Al-Shaarani, F., Gutub, A. Increasing Participants Using Counting-Based Secret Sharing via Involving Matrices and Practical Steganography. Arab J Sci Eng 47, 2455–2477 (2022). https://doi.org/10.1007/s13369-021-06165-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13369-021-06165-7