Abstract
Many practical complex networks, such as the Internet, WWW and social networks, are discovered to follow power-law distribution in their degree sequences, i.e., the number of nodes with degree \(i\) in these networks is proportional to \(i^{-\beta }\) for some exponential factor \(\beta > 0\). However, these networks also expose their vulnerabilities to a great number of threats such as adversarial attacks on the Internet, cyber-crimes on the WWW or malware propagations on social networks. Although power-law networks have been found robust under random attacks and vulnerable to intentional attacks via experimental observations, how to better understand their vulnerabilities from a theoretical point of view still remains open. In this paper, we study the vulnerability of power-law networks under random attacks and adversarial attacks using the in-depth probabilistic analysis on the theory of random power-law graph models. Our results indicate that power-law networks are able to tolerate random failures if their exponential factor \(\beta \) is \(<\)2.9, and they are more robust against intentional attacks if \(\beta \) is smaller. Furthermore, we reveal the best range \([1.8, 2.5]\) for the exponential factor \(\beta \) by optimizing the complex networks in terms of both their vulnerabilities and costs. When \(\beta < 1.8\), the network maintenance cost is very expensive, and when \(\beta > 2.5\) the network robustness is unpredictable since it depends on the specific attacking strategy.







Similar content being viewed by others
References
Aiello W, Chung F, Lu L (2000) A random graph model for massive graphs. In Proceedings of the thirty-second annual ACM symposium on Theory of computing, STOC ’00, pp 171–180, New York, NY, USA. ACM
Albert R, Albert I, Nakarado GL (2004) Structural vulnerability of the north american power grid. Phys Rev E 69(2):025103
Albert R, Jeong H, Barabasi A (2000) Error and attack tolerance of complex networks. Nature 406(6794):378–382
Alderson DL, Doyle JC (2010) Contrasting views of complexity and their implications for network-centric infrastructures. Trans Syst Man Cybern Part A 40(4):839–852
Barabasi AL, Albert R (1999) Emergence of scaling in random networks. Science 286(5439):509–512
Bollobás B, Riordan O, Spencer J, Tusnády G (2001) The degree sequence of a scale-free random graph process. Random Struct Algorithms 18(3):279–290
Chung F, Lu L (2002) Connected components in random graphs with given expected degree sequences. Ann Comb 6(2):125–145
Chung F, Lu L (2006) Concentration inequalities and martingale inequalities: a survey. Internet Math 3(1):79–127
Cohen R, Erez K, Ben-Avraham D, Havlin S (2000) Resilience of the internet to random breakdowns. Phys Rev Lett 85(21):4626
Dinh T, Thai M, Nguyen H (2014) Bound and exact methods for assessing link vulnerability in complex networks. J Comb Optim 28(1):3–24
Dinh TN, Xuan Y, Thai MT, Pardalos PM, Znati T (2011) IEEE/ACM Transactions on On new approaches of assessing network vulnerability: Hardness and approximation. Networking, PP(99):1
Doyle JC, Alderson DL, Li L, Low S, Roughan M, Shalunov S, Tanaka R, Willinger W (2005) The “robust yet fragile” nature of the Internet. Proc Natl Acad Sci USA, 102
Faloutsos M, Faloutsos P, Faloutsos C (1999) On power-law relationships of the internet topology. In Proceedings of the conference on Applications, technologies, architectures, and protocols for computer communication, SIGCOMM ’99, pp 251–262, New York, NY, USA. ACM
Gkantsidis C, Mihail M, Zegura E (2003) The markov chain simulation method for generating connected power law random graphs. In Proceedings of the 5th Workshop on Algorithm Engineering and Experiments (ALENEX). SIAM
Holme P, Kim BJ, Yoon CN, Han SK (2002) Attack vulnerability of complex networks. Phys Rev E 65(5):056109
Jamakovic A, Van Mieghem P (2008) On the robustness of complex networks by using the algebraic connectivity. In Proceedings of the 7th international IFIP-TC6 networking conference on AdHoc and sensor networks, wireless networks, next generation internet, NETWORKING’08, pp 183–194, Berlin, Heidelberg. Springer-Verlag
Kaiser M, Hilgetag CC (2004) Edge vulnerability in neural and metabolic networks. Biol Cybern 90:311–317. doi:10.1007/s00422-004-0479-1
Kitsak M, Havlin S, Paul G, Riccaboni M, Pammolli F, Stanley HE (2007) Betweenness centrality of fractal and nonfractal scale-free model networks and tests on real networks. Phys Rev E (Statistical, Nonlinear, and Soft Matter Physics) 75(5):056115
Lakhina A, Papagiannaki K, Crovella M, Diot C, Kolaczyk ED, Taft N (2004) Structural analysis of network traffic flows. In Proceedings of the joint international conference on Measurement and modeling of computer systems, SIGMETRICS ’04/Performance ’04, pp 61–72, New York NY, USA. ACM
Luciano, Rodrigues F, Travieso G, Boas VPR (2007) Characterization of complex networks: a survey of measurements. Adv Phys 56(1):167–242
Marin-Perianu RS, Scholten J, Havinga PJM, Hartel PH (2008) Cluster-based service discovery for heterogeneous wireless sensor networks. Int J Parallel Emerg Distrib Syst 23(4):325–346
Matisziw TC, Murray AT (2009) Modeling s-t path availability to support disaster vulnerability assessment of network infrastructure. Comput Oper Res 36(1):16–26 Part Special Issue: Operations Research Approaches for Disaster Recovery Planning
Mayo M, Abdelzaher A, Ghosh P (2015) Long-range degree correlations in complex networks. Comput Soc Netw 2(1):1–13
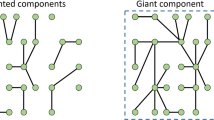
Molloy M, Reed B (1995) A critical point for random graphs with a given degree sequence. Random Struct Algorithms 6:161–179
Molloy M, Reed B (1998) The size of the giant component of a random graph with a given degree sequence. Comb Probab Comput 7(3):295–305
Satorras RP, Vespignani A (2002) Immunization of complex networks. Phys Rev E 65(3):036104
Smirnov M, Biersack EW, Blondia C, Bonaventure O, Casals O, Karlsson G, Pavlou G, Quoitin B, Roberts J, Stavrakakis I, Stiller B, Trimintzios P, Mieghem PV, editors (2003) Quality of Future Internet Services, COST Action 263 Final Report, volume 2856 of Lecture Notes in Computer Science. Springer
Ventresca M, Aleman D (2015) Efficiently identifying critical nodes in large complex networks. Comput Soc Netw 2(1):1–16
Yan G, Chen G, Eidenbenz S, Li N (2011) Malware propagation in online social networks: Nature, dynamics, and defense implications. In Proceedings of the 6th ACM Symposium on Information, Computer and Communications Security (AsiaCCS’11), Hongkong, China
Acknowledgments
This work is partially supported by NSF Career Award CNS-0953284 and NSF CCF-1422116.
Author information
Authors and Affiliations
Corresponding author
Additional information
Huiling Zhang and Yilin Shen are co-first authors.
Rights and permissions
About this article
Cite this article
Zhang, H., Shen, Y. & Thai, M.T. Robustness of power-law networks: its assessment and optimization. J Comb Optim 32, 696–720 (2016). https://doi.org/10.1007/s10878-015-9893-7
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10878-015-9893-7