Abstract
This paper presents a formal analysis of the device discovery phase of the Bluetooth wireless communication protocol. The performance of this process is the result of a complex interaction between several devices, some of which exhibit random behaviour. We use probabilistic model checking and, in particular, the tool PRISM to compute the best- and worst-case performance of device discovery: the expected time for the process to complete and the expected power consumption. We illustrate the utility of performing an exhaustive, low-level analysis to produce exact results in contrast to simulation techniques, where additional probabilistic assumptions must be made. We demonstrate an example of how seemingly innocuous assumptions can lead to incorrect performance estimations. We also analyse the effectiveness of improvements made between versions 1.1 and 1.2 of the Bluetooth specification.
Similar content being viewed by others
References
Bahar I., Frohm E., Gaona C., Hachtel G., Macii E., Pardo A., Somenzi F. (1997) Algebraic decision diagrams and their applications. Form. Methods Syst. Des.10(2/3): 171–206
Basagni, S., Bruno, R., Petrioli, C.: Device discovery in Bluetooth networks: scatternet perspective. In: Proceedings of Networking 2002, LNCS, vol. 2345, pp. 1087–1092. Springer, Berlin Heidelberg NewYork (2002)
BlueHoc—an open-source Bluetooth simulator.http://www-124.ibm.com/developerworks/opensource/bluehoc
Bluetooth specification, version 1.2, Bluetooth SIG,http://www.bluetooth.com (2003)
Bryant, R.: Binary decision diagrams and beyond: enabling technologies for formal verification. In: Proceedings of International Conference on Computer-Aided Design (ICCAD’95), pp. 236–243 (1995)
Clarke E., Fujita M., McGeer P., McMillan K., Yang J., Zhao X. (1997) Multi-terminal binary decision diagrams: an efficient data structure for matrix representation. Form. Methods Syst. Des. 10(2/3): 149–169
Daws C., Kwiatkowska M., Norman G. (2004) Automatic verification of the IEEE 1394 root contention protocol with KRONOS and PRISM. Int. J. Softw. Tools Technol. Transf. 5(2–3): 221–236
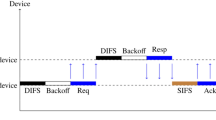
Duflot, M., Fribourg, L., Hérault, T., Lassaigne, R., Magniette, F., Messika, S., Peyronnet, S., Picaronny, C.: Probabilistic model checking of the CSMA/CD protocol using PRISM and APMC. In: Proceedings of the 4th Workshop on Automated Verification of Critical Systems (AVoCS’04). Electronic Notes in Theoretical Computer Science, vol. 128(6), pp. 195–214. Elsevier, Amsterdam (2004)
Kasten, O., Langheinrich, M.: First experiences with Bluetooth in the Smart its distributed sensor network. In: Proceedings of PACT’01 (2001)
Kwiatkowska, M., Norman, G.: Verifying randomized Byzantine agreement. In: Peled, D., Vardi, M. (eds.) Proceedings of Formal Techniques for Networked and Distributed Systems (FORTE’02). LNCS, vol. 2529, pp. 194–209. Springer, Berlin Heidelberg NewYork (2002)
Kwiatkowska, M., Norman, G., Parker, D.: Controller dependability analysis by probabilistic model checking. In: Proceedings of the 11th IFAC Symposium on Information Control Problems in Manufacturing (INCOM’04) (2004)
Kwiatkowska, M., Norman, G., Parker, D.: PRISM 2.0: a tool for probabilistic model checking. In: Proceedings of 1st International Conference on Quantitative Evaluation of Systems (QEST’04), pp. 322–323. IEEE Computer Society Press, Los Alamites(2004)
Kwiatkowska M., Norman G., Parker D., Sproston J. (2003). Performance analysis of probabilistic timed automata using digital clocks. In: Larsen K., Niebert P. (eds). Proceedings Formal Modeling and Analysis of Timed Systems (FORMATS’03). LNCS, vol. 2791, Springer, Berlin Heidelberg NewYork, pp. 105–120
Kwiatkowska M., Norman G., Segala R. (2001). Automated verification of a randomized distributed consensus protocol using Cadence SMV and PRISM. In: Berry G., Comon H., Finkel A. (eds). Proceedings of 13th International Conference on Computer Aided Verification (CAV’01). LNCS, vol. 2102, Springer, Berlin Heidelberg NewYork, pp. 194–206
Kwiatkowska, M., Norman, G., Sproston, J.: Probabilistic model checking of the IEEE 802.11 wireless local area network protocol. In: Hermanns, H., Segala, R. (eds.) Proceedings of 2nd Joint International Workshop on Process Algebra and Probabilistic Methods, Performance Modeling and Verification (PAPM/PROBMIV’02). LNCS, vol. 2399, pp. 169–187. Springer, Berlin Heidelberg NewYork (2002)
Kwiatkowska M., Norman G., Sproston J. (2003) Probabilistic model checking of deadline properties in the IEEE 1394 FireWire root contention protocol. Form. Asp. Comput. 14(3): 295–318
Kwiatkowska M., Norman G., Sproston J., Wang F. (2004). Symbolic model checking for probabilistic timed automata. In: Lakhnech Y., Yovine S. (eds). Joint Conference on Formal Modelling and Analysis of Timed Systems (FORMATS) and Formal Techniques in Real-Time and Fault Tolerant Systems (FTRTFT). LNCS, vol. 3253, Springer,Berlin Heidelberg NewYork, pp. 293–308
Norman G., Parker D., Kwiatkowska M., Shukla S. (2005) Evaluating the reliability of NAND multiplexing with PRISM. IEEE Trans. Comput.Aided Des. Integr. Circuits Syst. 24(10): 1629–1637
Norman G., Parker D., Kwiatkowska M., Shukla S., Gupta R. (2005) Using probabilistic model checking for dynamic power management. Form. Asp. Comput. 17(2): 160–176
Norman G., Shmatikov V. (2003). Analysis of probabilistic contract signing. In: Abdallah A., Ryan P., Schneider S. (eds). Proceedings of BCS-FACS Formal Aspects of Security (FASec’02). LNCS, vol. 2629, Springer,Berlin Heidelberg NewYork, pp. 81–96
ns-2: the Network Simulator. www.isi.edu/nsmam/ns
Peterson, B., Baldwin, R., Kharoufeh, J.: A specification-compatible Bluetooth inquiry simplification. In: Procecdings of Hawaii International Conference on System Sciences (HICSS’04) (2004)
PRISM Web site. www.cs.bham.ac.uk/~dxp/prism
Roy, A., Gopinath, K.: Improved probabilistic models for 802.11 protocol verification. In: Procecdings of the 17th International Conference on Computer Aided Verification (CAV’05). LNCS, vol. 3576, pp. 239–252. Springer,Berlin Heidelberg NewYork (2005)
Rutten J., Kwiatkowska M., Norman G., Parker D. (2004) Mathematical Techniques for analyzing concurrent and probabilistic systems, Panangaden, P., van Breugel,F. (eds.) CRM Monograph Series, vol. 23. American Mathematical Society, NewYork
Salonidis, T., Bhagwat, P., Tassiulas, L., LaMaire, R.: Proximity awareness and ad hoc network establishment in Bluetooth. Technical Report TR 2001-10. Institute of Systems Research, University of Maryland (2001)
Shmatikov V. (2004) Probabilistic model checking of an anonymity system. J. Comput. Secur. 12(3/4): 355–377
Siegemund F., Rohs M. (2002). Rendezvous layer protocols for Bluetooth-enabled smart devices. In: Proceedings of the Conference on Architecture of Computing Systems—Trends in Network and Pervasive Computing (ARCS’02). Springer, Berlin Heidelberg NewYork
Záruba, G., Gupta, V.: Simplified Bluetooth device discovery—analysis and simulation. In: Proceedings of the Hawaii International Conference on System Sciences (HICSS’04) (2004)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Duflot, M., Kwiatkowska, M., Norman, G. et al. A formal analysis of bluetooth device discovery. Int J Softw Tools Technol Transfer 8, 621–632 (2006). https://doi.org/10.1007/s10009-006-0014-x
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10009-006-0014-x