Abstract
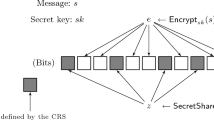
We revisit the following question: what are the minimal assumptions needed to construct statistically-hiding commitment schemes? Naor et al. show how to construct such schemes based on any one-way permutation. We improve upon this by showing a construction based on any approximable preimage-size one-way function. These are one-way functions for which it is possible to efficiently approximate the number of pre-images of a given output. A special case is the class of regular one-way functions where all points in the image of the function have the same (known) number of pre-images.
We also prove two additional results related to statistically-hiding commitment. First, we prove a (folklore) parallel composition theorem showing, roughly speaking, that the statistical hiding property of any such commitment scheme is amplified exponentially when multiple independent parallel executions of the scheme are carried out. Second, we show a compiler which transforms any commitment scheme which is statistically hiding against an honest-but-curious receiver into one which is statistically hiding even against a malicious receiver.
Article PDF
Similar content being viewed by others
References
N. Alon, L. Babai, A. Itai, A fast and simple randomized parallel algorithm for the maximal independent set problem, J. Algorithms 7(4), 567–583 (1986)
M. Bellare, S. Micali, How to sign given any trapdoor permutation, J. ACM 39(1), 214–233 (1992)
M. Bellare, R. Impagliazzo, M. Naor, Does parallel repetition lower the error in computationally sound protocols? in 38th FOCS, pp. 374–383, 1997
M. Blum, Coin flipping by telephone, in Advances in Cryptology—CRYPTO ’81, pp. 11–15, 1981
M. Blum, S. Micali, How to generate cryptographically-strong sequences of pseudorandom bits, SIAM J. Comput. 13(4), 850–864 (1984)
J. Boyar, S. Kurtz, M. Krentel, Discrete logarithm implementation of perfect zero-knowledge blobs, J. Cryptol. 2(2), 63–76 (1990)
G. Brassard, D. Chaum, C. Crépeau, Minimum disclosure proofs of knowledge, J. Comput. Syst. Sci. 37(2), 156–189 (1988)
J. Carter, M. Wegman, Universal classes of hash functions, J. Comput. Syst. Sci. 18(2), 143–154 (1979)
B. Chor, O. Goldreich, On the power of two-point based sampling, J. Complex. 5(1), 96–106 (1989)
I. Damgård, Collision free hash functions and public key signature schemes, in Eurocrypt ’87. LNCS, vol. 304 (Springer, Berlin, 1988), pp. 203–216.
I. Damgård, M. Pedersen, B. Pfitzmann, On the existence of statistically hiding bit commitment schemes and fail-stop signatures, J. Cryptol. 10(3), 163–194 (1997)
A. De Santis, M. Yung, On the design of provably-secure cryptographic hash functions, in EUROCRYPT: Advances in Cryptology: Proceedings of EUROCRYPT, pp. 412–431, 1990
O. Goldreich, Modern Cryptography, Probabilistic Proofs, and Pseudorandomness (Springer, Berlin, 1999)
O. Goldreich, Basic Tools. Foundations of Cryptography, vol. 1 (Cambridge University Press, Cambridge, 2001)
O. Goldreich, Basic Applications. Foundations of Cryptography, vol. 2 (Cambridge University Press, Cambridge, 2004)
O. Goldreich, A. Kahan, How to construct constant-round zero-knowledge proof systems for \(\mathcal{NP}\) , J. Cryptol. 9(3), 167–190 (1996)
O. Goldreich, L. Levin, Hard-core predicates for any one-way function, in 21st STOC, pp. 25–32, 1989
O. Goldreich, S. Goldwasser, S. Micali, On the cryptographic applications of random functions, in Advances in Cryptology—CRYPTO ’84, pp. 276–288, 1985
O. Goldreich, S. Goldwasser, S. Micali, How to construct random functions, J. ACM 33(4), 792–807 (1986)
O. Goldreich, S. Micali, A. Widgerson, How to play any mental game—a completeness theorem for protocols with honest majority, in 19th STOC, pp. 218–229, 1987
O. Goldreich, R. Impagliazzo, L. Levin, R. Venkatesan, D. Zuckerman, Security preserving amplification of hardness, in 31st FOCS, pp. 169–178, 1990
O. Goldreich, S. Micali, A. Widgerson, Proofs that yield nothing but their validity or all languages in \(\mathcal{NP}\) have zero-knowledge proof systems, J. ACM 38(1), 691–729 (1991)
O. Goldreich, H. Krawczyk, M. Luby, On the existence of pseudorandom generators, SIAM J. Comput. 22(6), 1163–1175 (1993)
S. Goldwasser, S. Micali, R. Rivest, A digital signature scheme secure against adaptive chosen-message attacks, SIAM J. Comput. 17(2), 281–308 (1988)
I. Haitner, O. Reingold, A new interactive hashing theorem, in 22nd Computational Complexity Conference, 2007. Draft of full version appears in www.wisdom.weizmann.ac.il/iftachh/papers/IneractiveHashing.pdf
I. Haitner, O. Reingold, Statistically-hiding commitment from any one-way function, in 39th STOC, 2007
I. Haitner, O. Horvitz, J. Katz, C. Koo, R. Morselli, R. Shaltiel, Reducing complexity assumptions for statistically-hiding commitment, in Advances in Cryptology—Eurocrypt 2005, pp. 58–77, 2005
S. Halevi, S. Micali, Practical and provably-secure commitment schemes from collision-free hashing, in Advances in Cryptology—CRYPTO ’96, pp. 201–215, 1996
J. Håstad, R. Impagliazzo, L. Levin, M. Luby, A pseudorandom generator from any one-way function, SIAM J. Comput. 28(4), 1364–1396 (1999)
R. Impagliazzo, M. Luby, One-way functions are essential for complexity-based cryptography, in 30th FOCS, pp. 230–235, 1989
R. Impagliazzo, S. Rudich, Limits on the provable consequences of one-way permutations, in 21st STOC, pp. 44–61, 1989
Y. Lindell, Parallel coin-tossing and constant-round secure two-party computation, J. Cryptol. 16(3), 143–184 (2003)
M. Naor, Bit commitment using pseudorandomness, J. Cryptol. 4(2), 151–158 (1991)
M. Naor, M. Yung, Universal one-way hash functions and their cryptographic applications, in 21st STOC, pp. 33–43, 1989
M. Naor, R. Ostrovsky, R. Venkatesan, M. Yung, Perfect zero-knowledge arguments for \(\mathcal{NP}\) using any one-way permutation, J. Cryptol. 11(2), 87–108 (1998)
M. Nguyen, S. Ong, S. Vadhan, Statistical zero-knowledge arguments for \(\mathcal{NP}\) from any one-way function, in 39th FOCS, 2006
R. Ostrovsky, R. Venkatesan, M. Yung, Secure commitment against a powerful adversary, in STACS, pp. 439–448, 1992
R. Ostrovsky, R. Venkatesan, M. Yung, Fair games against an all-powerful adversary, in DIMACS Series in Discrete Mathematics and Theoretical Computer Science, vol. 13, pp. 418–429, 1993
R. Raz, A parallel repetition theorem, SIAM J. Comput. 27(3), 763–803 (1998)
J. Rompel, One-way functions are necessary and sufficient for secure signatures, in 22nd STOC, pp. 387–394, 1990
A. Russell, Necessary and sufficient conditions for collision-free hashing, J. Cryptol. 8(2), 87–100 (1995)
A. Yao, Theory and application of trapdoor functions, in 23rd FOCS, pp. 80–91, 1982
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by Oded Goldreich
A preliminary version of this paper appeared at Haitner et al. (Advances in Cryptology—Eurocrypt 2005, pp. 58–77, 2005).
Research supported by US-Israel Binational Science Foundation grant 2002246.
Research of O.H. supported by U.S. Army Research Office award DAAD19-01-1-0494. Research of J.K. supported by NSF CAREER award #0447075.
Research supported by US-Israel Binational Science Foundation grant 2004329.
Rights and permissions
About this article
Cite this article
Haitner, I., Horvitz, O., Katz, J. et al. Reducing Complexity Assumptions for Statistically-Hiding Commitment. J Cryptol 22, 283–310 (2009). https://doi.org/10.1007/s00145-007-9012-8
Received:
Revised:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00145-007-9012-8