Abstract
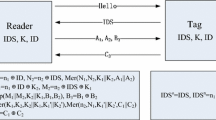
HB+ family protocols that based on LPN problem are effective and well suited for the Internet of Things. However, the HB+ family protocols have vulnerability on the man-in-the-middle attack. In this paper, we propose a new privacy preserving RFID authentication protocol based on the multiplication on \(Z_{2^k-1}\). By analyzing the differential property on \(Z_{2^{k}-1}\), we show that the protocol is resistant to the man-in-the-middle attack. Moreover, the performance analysis shows the protocol meets the demands of the large-scale RFID systems.
This work was supported by China national 863 project under No. 2013AA014002.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Alomair, B., Clark, A., Cuellar, J., Poovendran, R.: Scalable RFID systems: a privacy-preserving protocol with constant-time identification. IEEE Trans. Parallel Distrib. Syst. 23(8), 1536–1550 (2012)
Avoine, G., Carpent, X.: Yet another ultralightweight authentication protocol that is broken. In: Hoepman, J.-H., Verbauwhede, I. (eds.) RFIDSec 2012. LNCS, vol. 7739, pp. 20–30. Springer, Heidelberg (2013)
Molnar, D., Soppera, A., Wagner, D.: A scalable, delegatable pseudonym protocol enabling ownership transfer of RFID tags. In: Preneel, B., Tavares, S. (eds.) SAC 2005. LNCS, vol. 3897, pp. 276–290. Springer, Heidelberg (2006)
Bosley, C., Haralambiev, K., Nicolosi, A.: HBN: an HB-like protocol secure against man-in-the-middle attacks. IACR Cryptology ePrint Arch. 2011, 350 (2011)
Bringer, J., Chabanne, H., Dottax, E.: Hb++: a lightweight authentication protocol secure against some attacks. In: Second International Workshop on Security, Privacy and Trust in Pervasive and Ubiquitous Computing. SecPerU 2006, pp. 28–33. IEEE (2006)
Erguler, I., Anarim, E.: Scalability and security conflict for RFID authentication protocols. Wireless Pers. Commun. 59(1), 43–56 (2011)
Gilbert, H., Robshaw, M., Seurin, Y.: Good variants of HB+ are hard to find. In: Tsudik, G. (ed.) FC 2008. LNCS, vol. 5143, pp. 156–170. Springer, Heidelberg (2008)
Gilbert, H., Robshaw, M., Sibert, H.: Active attack against HB+: a provably secure lightweight authentication protocol. Electron. Lett. 41(21), 1169–1170 (2005)
Gilbert, H., Robshaw, M., Seurin, Y.: HB#: Increasing the security and efficiency of HB+. In: Smart, N.P. (ed.) EUROCRYPT 2008. LNCS, vol. 4965, pp. 361–378. Springer, Heidelberg (2008)
Juels, A.: RFID security and privacy: a research survey. IEEE J. Sel. Areas Commun. 24(2), 381–394 (2006)
Juels, A., Weis, S.A.: Authenticating pervasive devices with human protocols. In: Shoup, V. (ed.) CRYPTO 2005. LNCS, vol. 3621, pp. 293–308. Springer, Heidelberg (2005)
Katz, J., Shin, J.S., Smith, A.: Parallel and concurrent security of the HB and HB+ protocols. J. Cryptol. 23(3), 402–421 (2010)
Lyubashevsky, V., Masny, D.: Man-in-the-middle secure authentication schemes from LPN and weak PRFs. In: Canetti, R., Garay, J.A. (eds.) CRYPTO 2013, Part II. LNCS, vol. 8043, pp. 308–325. Springer, Heidelberg (2013)
Molnar, D., Wagner, D.: Privacy and security in library RFID: issues, practices, and architectures. In: Proceedings of the 11th ACM Conference on Computer and Communications Security, p. 219 (2004)
Ouafi, K., Overbeck, R., Vaudenay, S.: On the security of HB# against a man-in-the-middle attack. In: Pieprzyk, J. (ed.) asiacrypt 2008. LNCS, vol. 5350, pp. 108–124. Springer, Heidelberg (2008)
Song, B., Mitchell, C.J.: Scalable RFID security protocols supporting tag ownership transfer. Comput. Commun. 34(4), 556–566 (2011)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2015 Institute for Computer Sciences, Social Informatics and Telecommunications Engineering
About this paper
Cite this paper
Zhai, L., Wu, C. (2015). RFID Authentication Protocol Resistant to the Man-in-the-Middle Attack. In: Tian, J., Jing, J., Srivatsa, M. (eds) International Conference on Security and Privacy in Communication Networks. SecureComm 2014. Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, vol 153. Springer, Cham. https://doi.org/10.1007/978-3-319-23802-9_6
Download citation
DOI: https://doi.org/10.1007/978-3-319-23802-9_6
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-23801-2
Online ISBN: 978-3-319-23802-9
eBook Packages: Computer ScienceComputer Science (R0)