Abstract
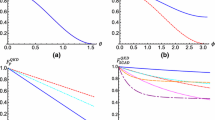
Kak’s three-stage protocol for quantum key distribution is revisited with special focus on its hitherto unknown strengths and weaknesses. It is shown that this protocol can be used for secure direct quantum communication. Further, the implementability of this protocol in the realistic situation is analyzed by considering various Markovian noise models. It is found that the Kak’s protocol and its variants in their original form can be implemented only in a restricted class of noisy channels, where the protocols can be transformed to corresponding protocols based on logical qubits in decoherence free subspace. Specifically, it is observed that Kak’s protocol can be implemented in the presence of collective rotation and collective dephasing noise, but cannot be implemented in its original form in the presence of other types of noise, like amplitude and phase damping noise. Further, the performance of the protocol in the noisy environment is quantified by computing average fidelity under various noise models, and subsequently a set of preferred states for secure communication in noisy environment have also been identified.



Similar content being viewed by others
Notes
The term “unconditional security” is frequently used in the literature of QKD assuming the devices used to implement are ideal and trustworthy.
An alternative definition exists in the literature [38] according to which Kak’s scheme should be viewed as a scheme for deterministic QKD since it does not involve block transmission. However, a deterministic QKD scheme can be adapted to perform direct secure quantum communication if the sender encrypts the message with a randomly chosen private key before sending it to the receiver using deterministic QKD and revealing the key only when she ensures the secure transmission of ciphertext.
Here, it may be noted that although Kak’s protocol in its original form would not work under the CD noise, there are techniques to use logical qubits and thus to exploit the advantage of a decoherence free subspace to realize Kak’s protocol in presence of CD noise [54, 56], but no such decoherence free subspace is known for the AD and PD noise.
References
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: International Conference on Computer System and Signal Processing, IEEE, pp. 175–179 (1984)
Ekert, A.K.: Quantum cryptography based on Bell’s theorem. Phys. Rev. Lett. 67, 661 (1991)
Bennett, C.H., Brassard, G., Mermin, N.D.: Quantum cryptography without Bell’s theorem. Phys. Rev. Lett. 68, 557 (1992)
Bennett, C.H.: Quantum cryptography using any two non orthogonal states. Phys. Rev. Lett. 68, 3121 (1992)
Goldenberg, L., Vaidman, L.: Quantum cryptography based on orthogonal states. Phys. Rev. Lett. 75, 1239 (1995)
Long, G.-L., Liu, X.-S.: Theoretically efficient high-capacity quantum-key-distribution scheme. Phys. Rev. A 65, 032302 (2002)
Boström, K., Felbinger, T.: Deterministic secure direct communication using entanglement. Phys. Rev. Lett. 89, 187902 (2002)
Deng, F.-G., Long, G.L., Liu, X.-S.: Two-step quantum direct communication protocol using the Einstein–Podolsky–Rosen pair block. Phys. Rev. A 68, 042317 (2003)
Degiovanni, I., Berchera, I.R., Castelletto, S., et al.: Quantum dense key distribution. Phys. Rev. A 69, 032310 (2004)
Deng, F.-G., Long, G.L.: Secure direct communication with a quantum one-time pad. Phys. Rev. A 69, 052319 (2004)
Lucamarini, M., Mancini, S.: Secure deterministic communication without entanglement. Phys. Rev. Lett. 94, 140501 (2005)
Shenoy, A., Pathak, A., Srikanth, R.: Quantum cryptography: key distribution and beyond. Quanta 6, 1–47 (2017)
Bennett, C.H., Bessette, F., Brassard, G., Salvail, L., Smolin, J.: Experimental quantum cryptography. J. Cryptol. 5, 3–28 (1992)
Zhao, Y., Qi, B., Ma, X., Lo, H.-K., Qian, L.: Experimental quantum key distribution with decoy states. Phys. Rev. Lett. 96, 070502 (2006)
Schmitt-Manderbach, T., Weier, H., Fürst, M., et al.: Experimental demonstration of free-space decoy-state quantum key distribution over 144 km. Phys. Rev. Lett. 98, 010504 (2007)
Lo, H.-K., Curty, M., Tamaki, K.: Secure quantum key distribution. Nat. Photon. 8, 595 (2014)
Hu, J.-Y., Yu, B., Jing, M.-Y., et al.: Experimental quantum secure direct communication with single photons. Light Sci. Appl. 5, e16144 (2016)
Zhang, W., Ding, D.-S., Sheng, Y.-B., et al.: Quantum secure direct communication with quantum memory. Phys. Rev. Lett. 118, 220501 (2017)
Zhu, F., Zhang, W., Sheng, Y., Huang, Y.: Experimental long-distance quantum secure direct communication. Sci. Bull. 62, 1519–1524 (2017)
Cao, Y., Li, Y.-H., Cao, Z., et al.: Direct counterfactual communication via quantum Zeno effect. Proc. Nat. Acad. Sci. 114, 4920–4924 (2017)
Kak, S.: A three-stage quantum cryptography protocol. Found. Phys. Lett. 19, 293–296 (2006)
Mandal, S., Macdonald, G., El Rifai, M., et al.: Multi-photon implementation of three-stage quantum cryptography protocol. In: 2013 International Conference on Information Networking (ICOIN), IEEE, pp. 6–11 (2013)
Chan, K.W.C., El Rifai, M., Verma, P., Kak, S., Chen, Y.: Security analysis of the multi-photon three-stage quantum key distribution. Int. J. Cryptogr. Inf. Secur. 5, 3/4 (2015)
Parakh, A.: A quantum oblivious transfer protocol. In: SPIE Optical Engineering + Applications of International Society for Optics and Photonics, pp. 883204–883204 (2013)
Lo, H.-K.: Insecurity of quantum secure computations. Phys. Rev. A 56, 1154 (1997)
Kang, M.-S., Hong, C.-H., Heo, J., Lim, J.-I., Yang, H.-J.: Quantum signature scheme using a single qubit rotation operator. Int. J. Theor. Phys. 54, 614–629 (2015)
Nikolopoulos, G.M.: Applications of single-qubit rotations in quantum public-key cryptography. Phys. Rev. A 77, 032348 (2008)
El Rifai, M., Verma, P. K.: An IEEE 802.11 quantum handshake using the three-stage protocol. In: 2014 23rd International Conference on Computer Communication and Networks (ICCCN), IEEE, pp. 1–6 (2014)
Kak, S., Chen, Y., Verma, P.: IAQC: The intensity-aware quantum cryptography protocol. arXiv preprint arXiv:1206.6778 (2012)
Kak, S.: Threshold quantum cryptography. arXiv preprint arXiv:1310.6333 (2013)
El Rifai, M., Punekar, N., Verma, P. K.: Implementation of an m-ary three-stage quantum cryptography protocol. In: Quantum Communications and Quantum Imaging XI vol. 8875, International Society for Optics and Photonics, p. 88750S (2013)
Darunkar, B., Verma, P. K.: The braided single-stage protocol for quantum secure communication. In: Quantum Information and Computation XII, vol. 9123, International Society for Optics and Photonics, p. 912308 (2014)
Wu, L., Chen, Y.: Three-stage quantum cryptography protocol under collective-rotation noise. Entropy 17, 2919–2931 (2015)
Parakh, A., Van Brandwijk, J.: Correcting rotational errors in three stage QKD. In: 2016 23rd International Conference on Telecommunications (ICT), IEEE, pp. 1–5 (2016)
Chitikela, S.: Noise analysis for two quantum cryptography protocols. arXiv preprint arXiv:1207.7281 (2012)
Pathak, A.: Elements of Quantum Computation and Quantum Communication. Taylor & Francis, New York (2013)
Shukla, C., Banerjee, A., Pathak, A.: Improved protocols of secure quantum communication using W states. Int. J. Theor. Phys. 52, 1914–1924 (2013)
Long, G.-L., Deng, F.-G., Wang, C., et al.: Quantum secure direct communication and deterministic secure quantum communication. Front. Phys. China 2, 251–272 (2007)
Yang, Y-y: A quantum secure direct communication protocol without quantum memories. Int. J. Theor. Phys. 53, 2216–2221 (2014)
Pathak, A.: Efficient protocols for unidirectional and bidirectional controlled deterministic secure quantum communication: different alternative approaches. Quantum Inf. Process. 14, 2195–2210 (2015)
Thapliyal, K., Pathak, A.: Applications of quantum cryptographic switch: various tasks related to controlled quantum communication can be performed using Bell states and permutation of particles. Quantum Inf. Process. 14, 2599–2616 (2015)
Banerjee, A., Shukla, C., Thapliyal, K., Pathak, A., Panigrahi, P.K.: Asymmetric quantum dialogue in noisy environment. Quantum Inf. Process. 16, 49 (2017)
Banerjee, A., Thapliyal, K., Shukla, C., Pathak, A.: Quantum conference. Quantum Inf. Process. 17, 161 (2018)
Shukla, C., Thapliyal, K., Pathak, A.: Semi-quantum communication: protocols for key agreement, controlled secure direct communication and dialogue. Quantum Inf. Process. 16, 295 (2017)
Thapliyal, K., Sharma, R.D., Pathak, A.: Protocols for quantum binary voting. Int. J. Quantum Inf. 15, 1750007 (2017)
Sharma, R.D., Thapliyal, K., Pathak, A.: Quantum sealed-bid auction using a modified scheme for multiparty circular quantum key agreement. Quantum Inf. Process. 16, 169 (2017)
Thapliyal, K., Sharma, R. D., Pathak, A.: Orthogonal-state-based and semi-quantum protocols for quantum private comparison in noisy environment. arXiv preprint arXiv:1608.00101 (2016)
Breuer, H.-P., Petruccione, F.: The Theory of Open Quantum Systems. Oxford University Press, Oxford (2002)
Nielsen, M.A., Chuang, I.L.: Quantum Computation and Quantum Information. Cambridge University Press, Cambridge (2010)
Preskill, J.: Lecture notes for physics 229: quantum information and computation. Calif. Inst. Technol. 12, 14 (1998)
Thapliyal, K., Banerjee, S., Pathak, A., Omkar, S., Ravishankar, V.: Quasiprobability distributions in open quantum systems: spin-qubit systems. Ann. Phys. 362, 261–286 (2015)
Zanardi, P., Rasetti, M.: Noiseless quantum codes. Phys. Rev. Lett. 79, 3306 (1997)
Bourennane, M., Eibl, M., Gaertner, S., et al.: Decoherence-free quantum information processing with four-photon entangled states. Phys. Rev. Lett. 92, 107901 (2004)
Sharma, R.D., Thapliyal, K., Pathak, A., Pan, A.K., De, A.: Which verification qubits perform best for secure communication in noisy channel? Quantum Inf. Process. 15, 1703–1718 (2016)
Fischer, D.G., Mack, H., Cirone, M.A., Freyberger, M.: Enhanced estimation of a noisy quantum channel using entanglement. Phys. Rev. A 64, 022309 (2001)
Li, X.-H., Deng, F.-G., Zhou, H.-Y.: Efficient quantum key distribution over a collective noise channel. Phys. Rev. A 78, 022321 (2008)
Thapliyal, K., Pathak, A., Banerjee, S.: Quantum cryptography over non-Markovian channels. Quantum Inf. Process. 16, 115 (2017)
Boileau, J.C., Gottesman, D., Laflamme, R., Poulin, D., Spekkens, R.W.: Robust polarization-based quantum key distribution over a collective-noise channel. Phys. Rev. Lett. 92, 017901 (2004)
Sharma, V., Thapliyal, K., Pathak, A., Banerjee, S.: A comparative study of protocols for secure quantum communication under noisy environment: single-qubit-based protocols versus entangled-state-based protocols. Quantum Inf. Process. 15, 4681–4710 (2016)
Acknowledgements
KT thanks CSIR, India, for the support provided through Senior Research Fellowship. AP thanks Defense Research & Development Organization (DRDO), India, for the support provided through the Project Number ERIP/ER/ 1403163/M/01/1603.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Thapliyal, K., Pathak, A. Kak’s three-stage protocol of secure quantum communication revisited: hitherto unknown strengths and weaknesses of the protocol. Quantum Inf Process 17, 229 (2018). https://doi.org/10.1007/s11128-018-2001-z
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-018-2001-z